Last Update 15 hours ago Total Questions : 125
The Oracle WebLogic Server 12c: Advanced Administrator II content is now fully updated, with all current exam questions added 15 hours ago. Deciding to include 1z0-134 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 1z0-134 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 1z0-134 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Oracle WebLogic Server 12c: Advanced Administrator II practice test comfortably within the allotted time.
Your developers have decided to use a deployment plan with their applications that will be deployed by WebLogic administrators into one or more WebLogic Server production environments.
Which two primary goals can be accomplished by leveraging a deployment plan? (Choose two.)
You successfully configured a new dynamic cluster but haven’t launched any of the dynamic servers. You want to change the configuration for one specific server.
Which parameter can you modify for that server before starting up the dynamic clustered servers for the first time?
You are considering targeting your JMS servers to dynamic clusters to benefit from dynamic scaling. However, you have been advised to keep in mind some of the associated limitations.
What are two valid limitations and considerations for clustered JMS services? (Choose two.)
Review the diagram below. It depicts the following:
A WebLogic domain that consists of two WebLogic clusters that are each included in a Coherence cluster
The Coherence cluster includes a configuration for Coherence*Web HTTP session storage
An application deployed on cluster 1 that is configured to use Coherence*Web
A client is using a web browser to interact with the application on cluster 1 (via a proxy)
The client’s HTTP session is stored by Coherence*Web on the server in the upper right-hand corner
The server where the client’s HTTP session is stored crashes
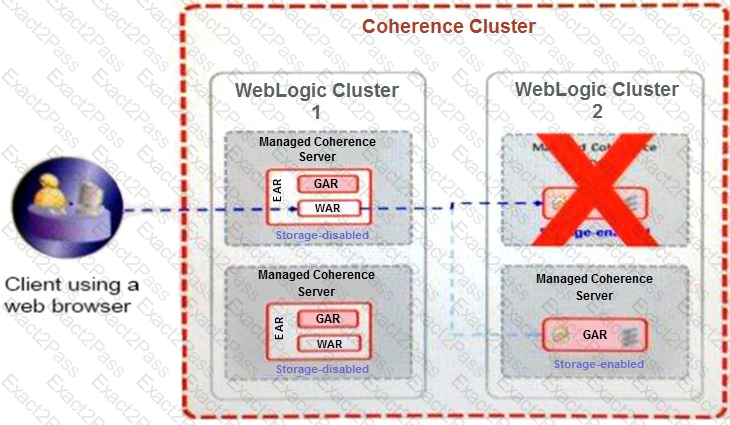
Assuming the next request for an HTTP session attribute is a new attribute that is not stored in a near-cache, the client’s session attribute is fetched from the remaining storage-enabled server in cluster 2.
Why is the session attribute retrieved from this other server’s cache? (Choose the best answer.)
You are responsible for creating scripts to use Node Manager with a WebLogic Server domain.
Which four statements correctly describe the WLST command: nmEnroll? (Choose four.)
The administration server is a major component of a WebLogic domain. I need to make available a standby administration server in case the main administration server in the domain crashes.
Which utility will help me in doing this? (Choose the best answer.)
You created a user and group using the WebLogic Server default authentication provider.
Where are these principals stored? (Choose the best answer.)

