Last Update 1 day ago Total Questions : 434
The Developing Applications using Cisco Core Platforms and APIs (DEVCOR) content is now fully updated, with all current exam questions added 1 day ago. Deciding to include 350-901 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 350-901 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 350-901 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Developing Applications using Cisco Core Platforms and APIs (DEVCOR) practice test comfortably within the allotted time.
Which two statements about a stateless application are true? (Choose two.)
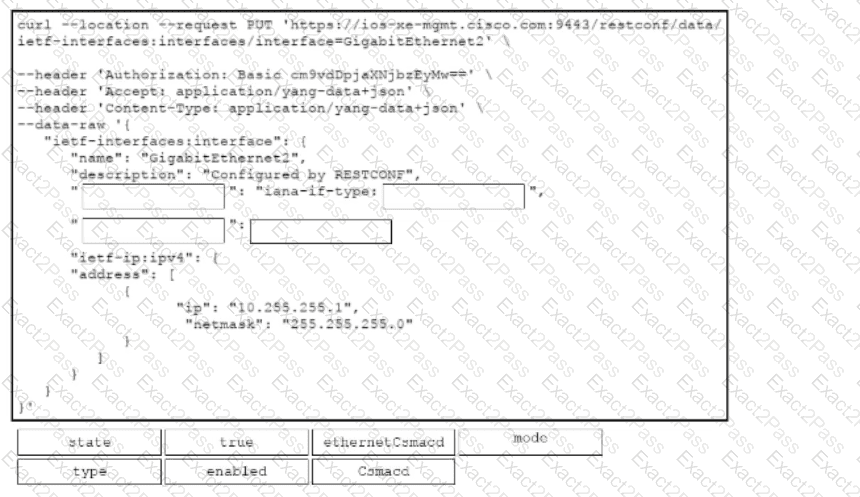
Drag and drop the code snippets from the bottom onto the blanks in the cURL script that uses RESTCONF to update an interface on a Cisco IOS XE device. Not all options are used.
Refer to the exhibit.
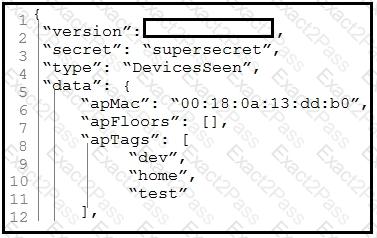
Which parameter is missing from the JSON response to confirm the API version that is
used?
A developer must recommend an appropriate tool to deploy a configuration to hundreds of servers. The configuration management solution must meet these requirements.
• The servers must initiate the connection to obtain updates
• The configuration must be defined in a declarative style
Which tool should be used?
Where mus! the data be encrypted to ensure end-to-end encryption when using an API?
A developer in a learn of distributed authors is working on code in an isolated Git branch named ' update4a2f5464771 The developer attempts to merge the new code with a branch named ’dvcapp2a3f1564733 ' however the merge operation encounters a conflict error during the process. Which Git command must the developer use to exit from the merge process and return the branch to the previous state?
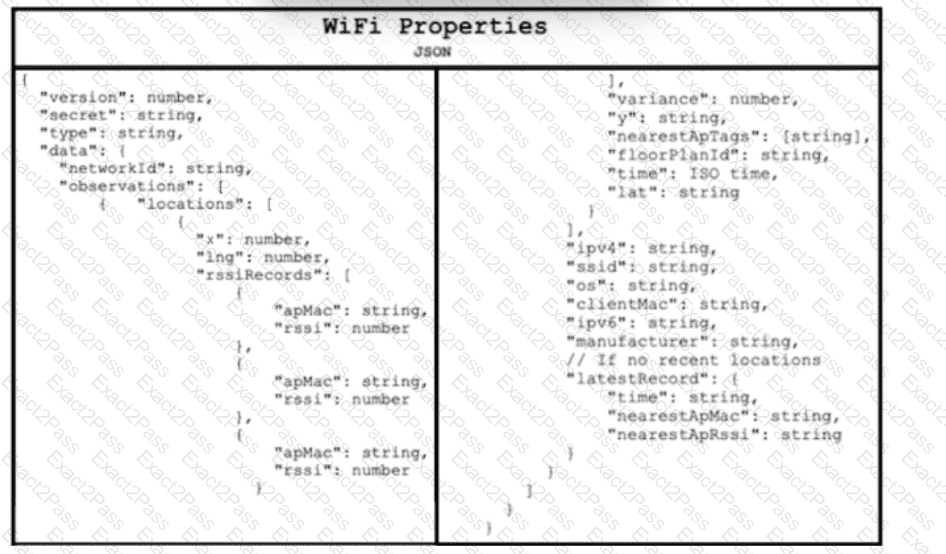
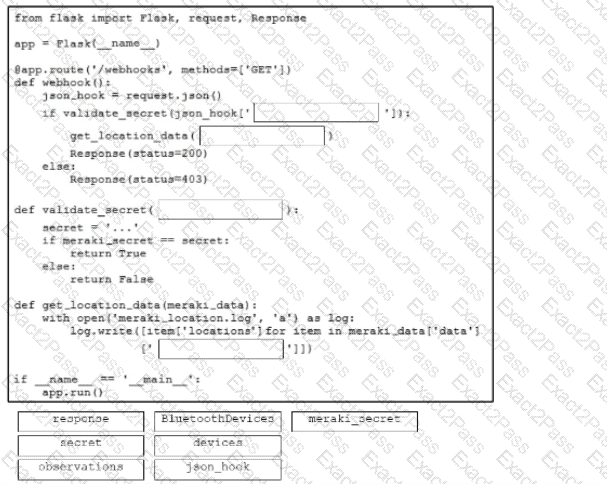
Refer to the exhibit. Drag and drop the code snippets from the bottom onto the blanks in the Python script to retrieve location data from the Cisco Meraki Location API by using a webhook receiver. Not all options are used.