Last Update 15 hours ago Total Questions : 64
The Certified Kubernetes Security Specialist (CKS) content is now fully updated, with all current exam questions added 15 hours ago. Deciding to include CKS practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our CKS exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these CKS sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Certified Kubernetes Security Specialist (CKS) practice test comfortably within the allotted time.
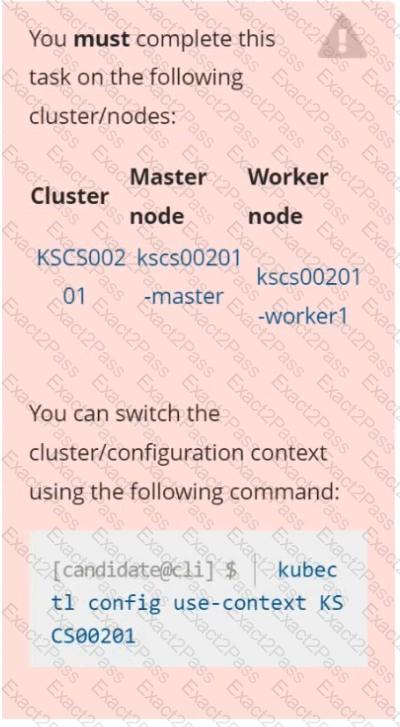
You must complete this task on the following cluster/nodes:
Cluster: trace
Master node: master
Worker node: worker1
You can switch the cluster/configuration context using the following command:
[desk@cli] $ kubectl config use-context trace
Given : You may use Sysdig or Falco documentation.
Task:
Use detection tools to detect anomalies like processes spawning and executing something weird frequently in the single container belonging to Pod tomcat .
Two tools are available to use:
1. falco
2. sysdig
Tools are pre-installed on the worker1 node only.
Analyse the container’s behaviour for at least 40 seconds, using filters that detect newly spawning and executing processes.
Store an incident file at /home/cert_masters/report , in the following format:
[timestamp],[uid] ,[processName]
Note: Make sure to store incident file on the cluster ' s worker node, don ' t move it to master node.
Secrets stored in the etcd is not secure at rest, you can use the etcdctl command utility to find the secret value
for e.g:-
ETCDCTL_API=3 etcdctl get /registry/secrets/default/cks-secret --cacert= " ca.crt " --cert= " server.crt " --key= " server.key "
Output
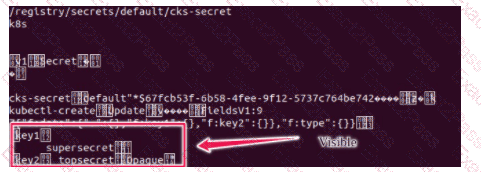
Using the Encryption Configuration, Create the manifest, which secures the resource secrets using the provider AES-CBC and identity, to encrypt the secret-data at rest and ensure all secrets are encrypted with the new configuration.
Context
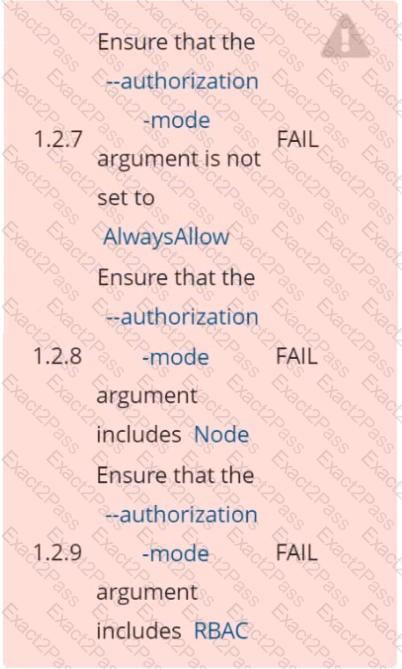
A CIS Benchmark tool was run against the kubeadm-created cluster and found multiple issues that must be addressed immediately.
Task
Fix all issues via configuration and restart the affected components to ensure the new settings take effect.
Fix all of the following violations that were found against the API server:
Fix all of the following violations that were found against the Kubelet:
Fix all of the following violations that were found against etcd:
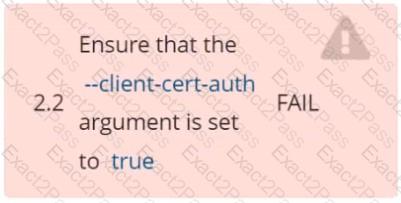
Fix all issues via configuration and restart the affected components to ensure the new setting takes effect.
Fix all of the following violations that were found against the API server :-
a. Ensure that the RotateKubeletServerCertificate argument is set to true .
b. Ensure that the admission control plugin PodSecurityPolicy is set .
c. Ensure that the --kubelet-certificate-authority argument is set as appropriate.
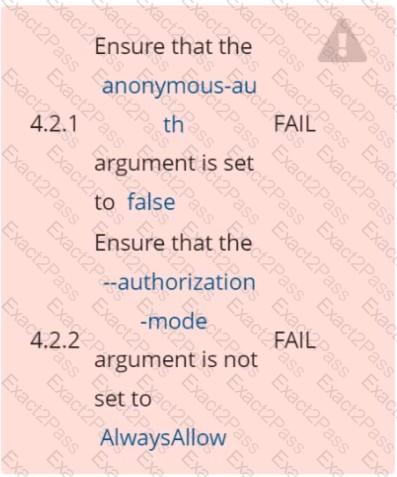
Fix all of the following violations that were found against the Kubelet :-
a. Ensure the --anonymous-auth argument is set to false .
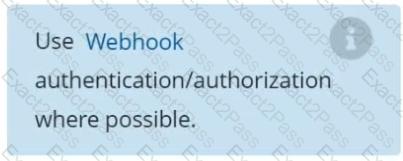
b. Ensure that the --authorization-mode argument is set to Webhook.
Fix all of the following violations that were found against the ETCD :-
a. Ensure that the -- auto -tls argument is not set to true
b. Ensure that the --peer- auto -tls argument is not set to true
Hint: Take the use of Tool Kube-Bench
Documentation Ingress, Service, NGINX Ingress Controller
You must connect to the correct host . Failure to do so may result in a zero score.
[candidate@base] $ ssh cks000032
Context
You must expose a web application using HTTPS routes.
Task
Create an Ingress resource named web in the prod namespace and configure it as follows:
. Route traffic for host web.k8s.local and all paths to the existing Service web
. Enable TLS termination using the existing Secret web-cert.
. Redirect HTTP requests to HTTPS .
You can test your Ingress configuration with the following command:
[candidate@cks000032]$ curl -L http://web.k8s.local
Context
Your organization’s security policy includes:
ServiceAccounts must not automount API credentials
ServiceAccount names must end in " -sa "
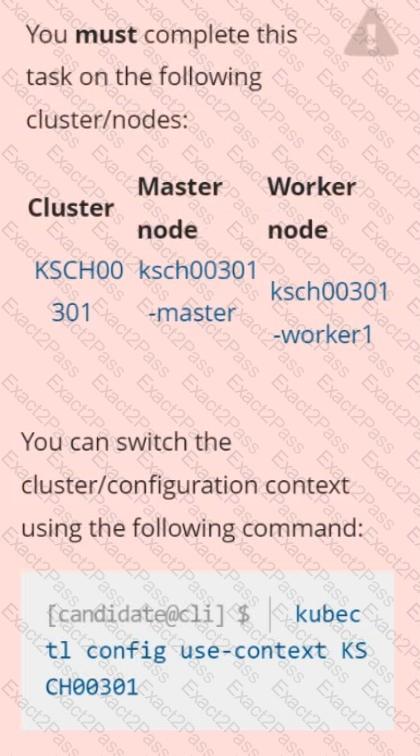
The Pod specified in the manifest file /home/candidate/KSCH00301 /pod-m
nifest.yaml fails to schedule because of an incorrectly specified ServiceAccount.
Complete the following tasks:
Task
1. Create a new ServiceAccount named frontend-sa in the existing namespace qa. Ensure the ServiceAccount does not automount API credentials.
2. Using the manifest file at /home/candidate/KSCH00301 /pod-manifest.yaml, create the Pod.
3. Finally, clean up any unused ServiceAccounts in namespace qa.
Enable audit logs in the cluster, To Do so, enable the log backend, and ensure that
1. logs are stored at / var /log/kubernetes/kubernetes-logs.txt.
2. Log files are retained for 5 days.
3. at maximum, a number of 10 old audit logs files are retained.
Edit and extend the basic policy to log:
1. Cronjobs changes at RequestResponse
2. Log the request body of deployments changes in the namespace kube-system.
3. Log all other resources in core and extensions at the Request level.
4. Don ' t log watch requests by the " system:kube-proxy " on endpoints or

