Last Update 2 hours ago Total Questions : 396
The CompTIA Data+ Certification Exam content is now fully updated, with all current exam questions added 2 hours ago. Deciding to include DA0-001 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our DA0-001 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these DA0-001 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any CompTIA Data+ Certification Exam practice test comfortably within the allotted time.
You are working with a dataset and need to swap the values in rows with those in columns.
What action do you need to perform?
A large data download was divided into two smaller files. Which of the following describes the best way to fix this issue?
An analyst is working with a data set that lists individuals ' first and last names in separate columns. Which of the following processes should the analyst use to combine the first and last names into a single spreadsheet cell?
An analyst needs to join two data sets that compare vehicle weights. One data set is in pounds, and the other has various units of measure. Which of the following should the analyst do first to the data prior to any type of join?
Given the following data:
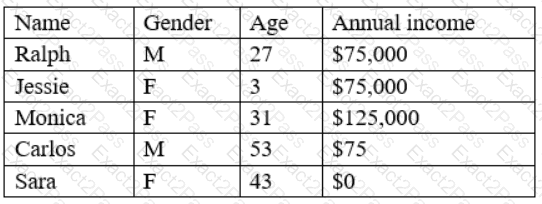
Which of the following BEST describes the data set?
Which of the following is an example of a at flat file?
Joe. an analyst. tests the loading time on a dashboard he is preparing to go live and finds it is slower than he would like. Which of the following must occur to decrease the loading time?
What analytics suite is offered by Microsoft and directly integrates with SQL Server Databases?
Which of the following is an example of structured data?
A data analyst is working with a team to create a dashboard for a client who requires on-demand access. Which of the following is the best delivery method to support the clients’ requirement?

