Last Update 12 hours ago Total Questions : 99
The Fortinet NSE 7 - SD-WAN 7.2 content is now fully updated, with all current exam questions added 12 hours ago. Deciding to include NSE7_SDW-7.2 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our NSE7_SDW-7.2 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these NSE7_SDW-7.2 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Fortinet NSE 7 - SD-WAN 7.2 practice test comfortably within the allotted time.
Which best describes the SD-WAN traffic shaping mode that bases itself on a percentage of available bandwidth?
Refer to the exhibit.
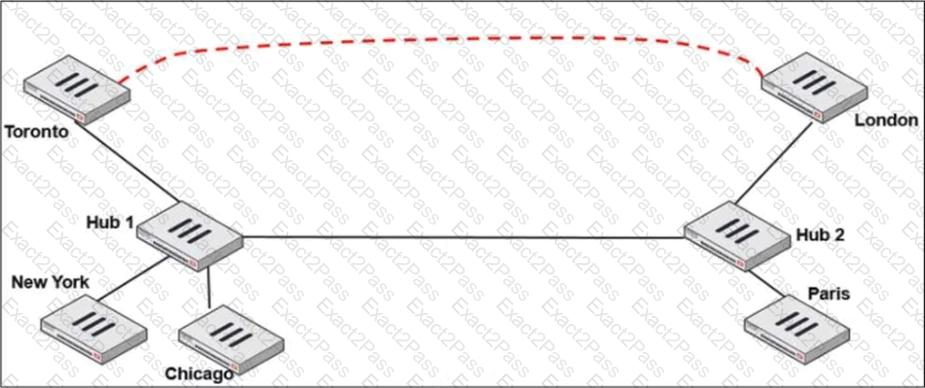
Two hub-and-spoke groups are connected through a site-to-site IPsec VPN between Hub 1 and Hub 2.
Which two configuration settings are required for Toronto and London spokes to establish an ADVPN shortcut? (Choose two.)
Which are two benefits of using CLI templates in FortiManager? (Choose two.)
Within IPsec tunnel templates available on FortiManager. which template will you use to configure static tunnels for a hub and spoke topology?
Which diagnostic command can you use to show the configured SD-WAN zones and their assigned members?
Refer to the exhibit.
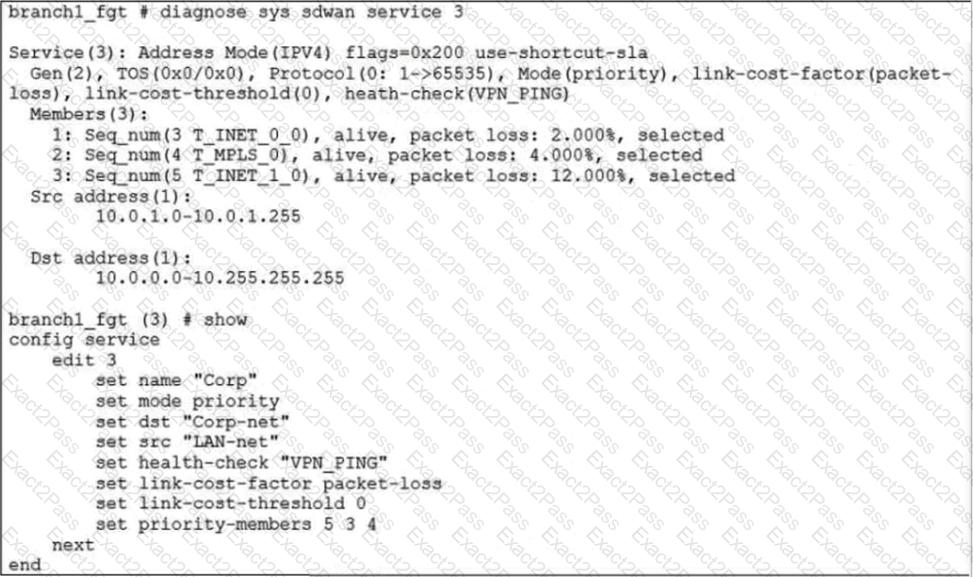
The exhibit shows the SD-WAN rule status and configuration.
Based on the exhibit, which change in the measured packet loss will make T_INET_1_0 the new preferred member?
Refer to the exhibit.
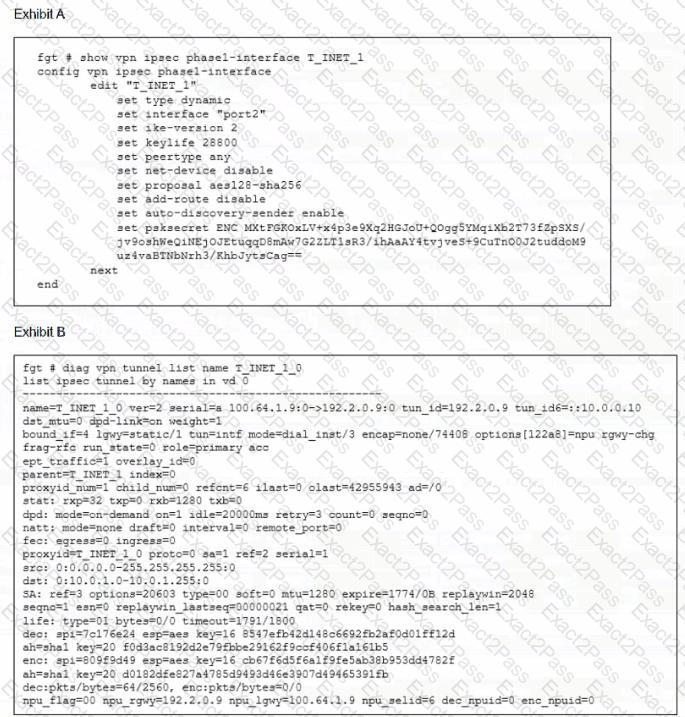
Which two statements about the IPsec VPN configuration and the status of the IPsec VPN tunnel are true? (Choose two.)

