Last Update 9 hours ago Total Questions : 464
The CompTIA PenTest+ Certification Exam content is now fully updated, with all current exam questions added 9 hours ago. Deciding to include PT0-002 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our PT0-002 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these PT0-002 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any CompTIA PenTest+ Certification Exam practice test comfortably within the allotted time.
A mail service company has hired a penetration tester to conduct an enumeration of all user accounts on an SMTP server to identify whether previous staff member accounts are still active. Which of the following commands should be used to accomplish the goal?
A compliance-based penetration test is primarily concerned with:
Which of the following provides a matrix of common tactics and techniques used by attackers along with recommended mitigations?
A penetration tester has completed an analysis of the various software products produced by the company under assessment. The tester found that over the past several years the company has been including vulnerable third-party modules in multiple products, even though the quality of the organic code being developed is very good. Which of the following recommendations should the penetration tester include in the report?
Which of the following protocols or technologies would provide in-transit confidentiality protection for emailing the final security assessment report?
A penetration tester is enumerating shares and receives the following output:
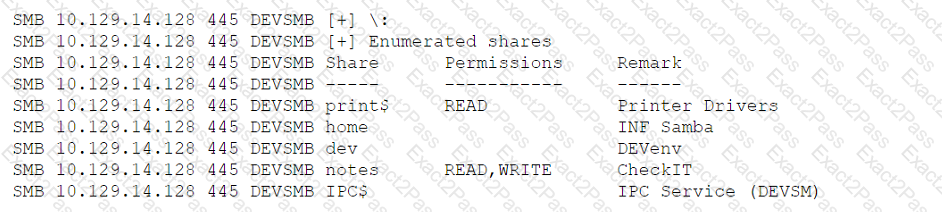
Which of the following should the penetration tester enumerate next?

