Last Update 1 day ago Total Questions : 388
The Microsoft Security Operations Analyst content is now fully updated, with all current exam questions added 1 day ago. Deciding to include SC-200 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our SC-200 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these SC-200 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Microsoft Security Operations Analyst practice test comfortably within the allotted time.
You need to recommend a solution to meet the technical requirements for the Azure virtual machines. What should you include in the recommendation?
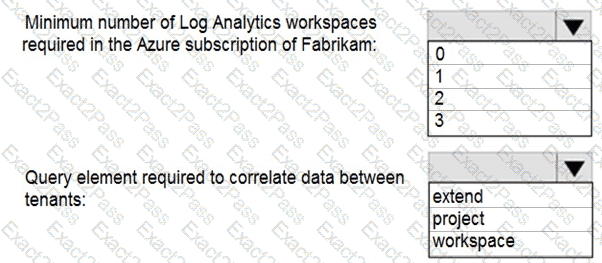
You need to implement Azure Sentinel queries for Contoso and Fabrikam to meet the technical requirements.
What should you include in the solution? To answer, select the appropriate options in the answer area .
NOTE: Each correct selection is worth one point.
The issue for which team can be resolved by using Microsoft Defender for Endpoint?
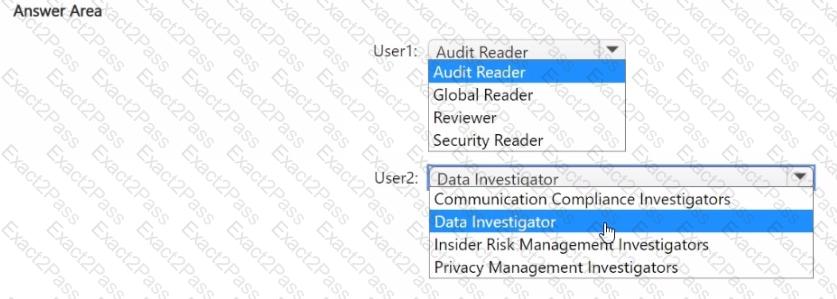
You have a Microsoft 365 E5 subscription that uses Microsoft Defender XDR and contains two users named User1 and User2.
You need to ensure that the users can perform searches by using the Microsoft Purview portal. The solution must meet the following requirements:
• Ensure that User1 can search the Microsoft Purview Audit service logs and review the Microsoft Purview Audit service configuration.
• Ensure that User2 can search Microsoft Exchange Online mailboxes.
• Follow the principle of least privilege.
To which Microsoft Purview role group should you add each user? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have a Microsoft 365 subscription. You have the following KQL query.
DeviceEvents
| where ActionType == " AntivirusDetection*
You need to ensure that you can create a Microsoft Defender XDR custom detection rule by using the query.
What should you add to the query?
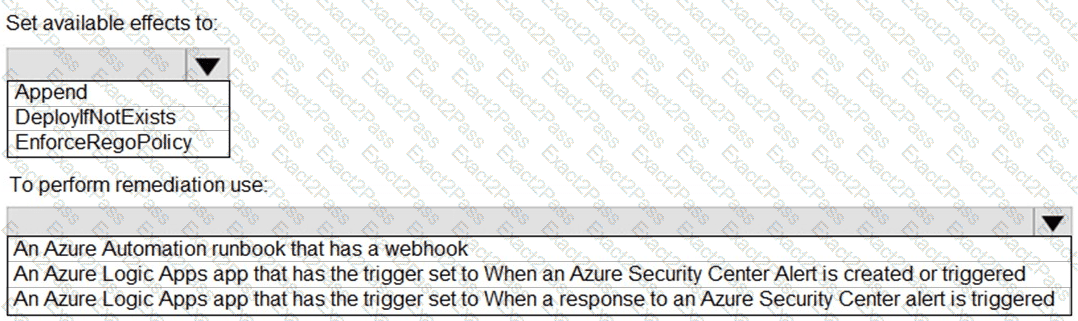
You have an Azure subscription that uses Azure Defender.
You plan to use Azure Security Center workflow automation to respond to Azure Defender threat alerts.
You need to create an Azure policy that will perform threat remediation automatically.
What should you include in the solution? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
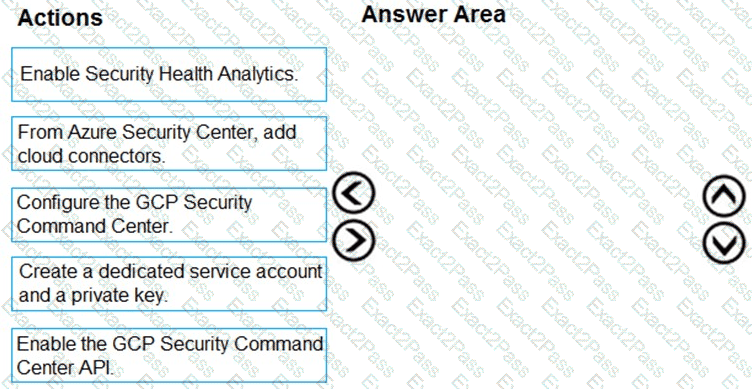
You have resources in Azure and Google cloud.
You need to ingest Google Cloud Platform (GCP) data into Azure Defender.
In which order should you perform the actions? To answer, move all actions from the list of actions to the answer area and arrange them in the correct order.
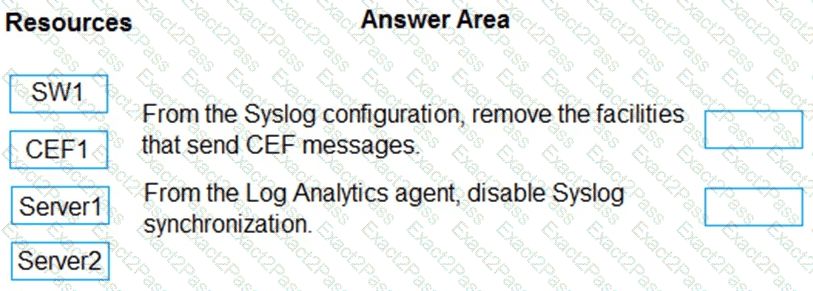
You have the resources shown in the following table.
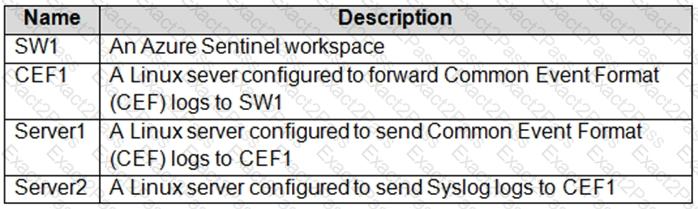
You need to prevent duplicate events from occurring in SW1.
What should you use for each action? To answer, drag the appropriate resources to the correct actions. Each resource may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
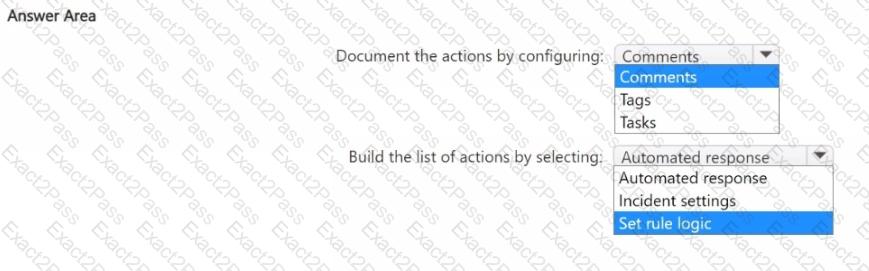
You have an Azure subscription that contains a Microsoft Sentinel workspace named WS1.
You need to ensure that the incidents in WS1 include a list of actions that must be performed. The solution must meet the following requirements:
• Ensure that you can build a tailored list of actions for each type of incident.
• Minimize administrative effort.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have an Azure subscription that has Microsoft Defender for Cloud enabled.
You have a virtual machine that runs Windows 10 and has the Log Analytics agent installed.
You need to simulate an attack on the virtual machine that will generate an alert.
What should you do first?

