Last Update 11 hours ago Total Questions : 299
The Implementing and Configuring Cisco Identity Services Engine (SISE) v4.0 (300-715 SISE) content is now fully updated, with all current exam questions added 11 hours ago. Deciding to include 300-715 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 300-715 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 300-715 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Implementing and Configuring Cisco Identity Services Engine (SISE) v4.0 (300-715 SISE) practice test comfortably within the allotted time.
An organization is hosting a conference and must make guest accounts for several of the speakers attending. The conference ended two days early but the guest accounts are still being used to access the network. What must be configured to correct this?
A network administrator is configuring a secondary cisco ISE node from the backup configuration of the primary cisco ISE node to create a high availability pair The Cisco ISE CA certificates and keys must be manually backed up from the primary Cisco ISE and copied into the secondary Cisco ISE Which command most be issued for this to work?
Which two actions occur when a Cisco ISE server device administrator logs in to a device? (Choose two)
Which command displays all 802 1X/MAB sessions that are active on the switch ports of a Cisco Catalyst switch?
Which RADIUS attribute is used to dynamically assign the Inactivity active timer for MAB users from the Cisco ISE node?
An organization wants to enable web-based guest access for both employees and visitors The goal is to use a single portal for both user types Which two authentication methods should be used to meet this requirement? (Choose two )
What is a characteristic of the UDP protocol?
An engineer is configuring ISE for network device administration and has devices that support both protocols. What are two benefits of choosing TACACS+ over RADUs for these devices? (Choose two.)
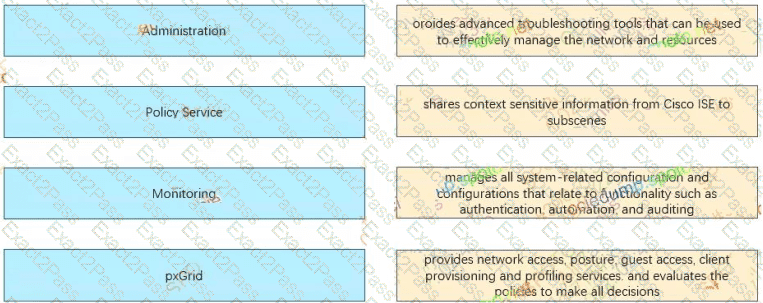
Select and Place
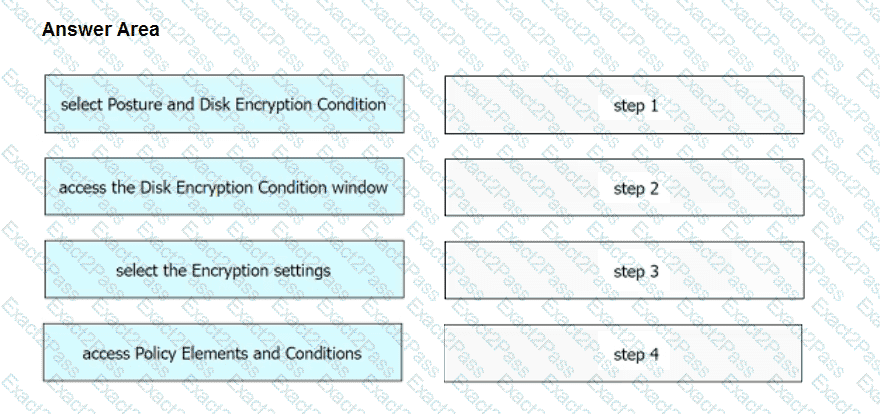
An engineer needs to configure a compliance policy on Cisco ISE to ensure that the latest encryption software is running on the C drive of all endpoints. Drag and drop the configuration steps from the left into the sequence on the right to accomplish this task.