We have coached hundreds of network engineers and enterprise architects through this challenging professional-tier milestone. The candidates who fall short on exam day are almost always those who relied on low-quality, static brain dumps—materials that simply cannot prepare you for complex infrastructure deployment. At Exact2Pass, our ecosystem targets the underlying technical rationale instead. Our Cisco 350-401 ENCOR exam prep delivers comprehensive engineering breakdowns for every complex configuration query. You will master the actual networking mechanics instead of just memorizing answers. We map out advanced routing protocols, SD-WAN control planes, and enterprise wireless deployments step by step. That is how you bridge the gap between hoping for a passing score and knowing you can execute high-level infrastructure tasks inside the Pearson VUE testing environment.
Which characteristic applies to Cisco SD-Access?
What is two characteristic of Cisco DNA Center and vManage northbound APIs?
What does the statement print(format(0.8, \0% ' )) display?
Which two southbound interfaces originate from Cisco Catalyst Center (formerly DNA Center) and terminate at fabric underlay switches ' ? (Choose two.)
With IGMPv2, which multicast group address does the IGMP querier use to send query messages to all hosts on the LAN?
What is a fact about Cisco EAP-FAST?
What is one main REST security design principle?
In a Cisco SD-Access wireless architecture, which device manages endpoint ID to edge node bindings?
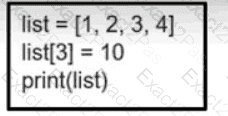
Refer to the exhibit. What is the value of the variable list after the code is run?

