Last Update 14 hours ago Total Questions : 100
The Logical Operations CyberSec First Responder content is now fully updated, with all current exam questions added 14 hours ago. Deciding to include CFR-210 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our CFR-210 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these CFR-210 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Logical Operations CyberSec First Responder practice test comfortably within the allotted time.
The incident response team needs to track which user last connected to a specific Windows domain controller. Which of the following is the BEST way to identify that specific user?
An attacker has exfiltrated the SAM file from a Windows workstation. Which of the following attacks is MOST likely being perpetrated?
Which of the following are legally compliant forensics applications that will detect ADS or a file with an incorrect file extension? (Choose two.)
Which of the following technologies is used as mitigation to XSS attacks?
A SOC analyst reviews vendor security bulletins and security blog articles against the company’s deployed system and software base. Based on current attack patterns, three vulnerabilities, including a zero-day vulnerability, have been upgraded to high priority. Which of the following should the SOC analyst recommend? (Choose two.)
Which of the following is an automated password cracking technique that uses a combination of upper and lower case letters, 0-9 numbers, and special characters?
An incident responder is asked to work with the IT department to address patch management issues with the company servers. Which of the following is the BEST source for the incident responder to obtain the CVEs for the latest industry-recognized patches?
A company website was hacked via the SQL query below:
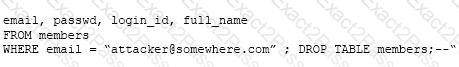
Which of the following did the hackers perform?
From a compromised system, an attacker bypasses a proxy server and sends a large amount of data to a remote location. A security analyst is tasked with finding the conduit that was used by the attacker to bypass the proxy. Which of the following Windows tools should be used to find the conduit?
During review of a company’s web server logs, the following items are discovered:
2015-03-01 03:32:11 www.example.com/index.asp?id=-999 or 1=convert(int,@@version)—
2015-03-01 03:35:33 www.example.com/index.asp?id=-999 or 1=convert(int,db_name())—
2015-03-01 03:38:25 www.example.com/index.asp?id=-999 or 1=convert(int,user_name())—
Which of the following is depicted in the log example above?

