A systems administrator is troubleshooting performance issues with a Windows VDI environment. Users have reported that VDI performance has been slow since the images were upgraded from Windows 7 to Windows 10.
This VDI environment is used to run simple tasks, such as Microsoft Office. The administrator investigates the virtual machines and finds the following settings:
4 vCPU
16GB RAM
10Gb networking
256MB frame buffer
Which of the following MOST likely needs to be upgraded?
A systems administrator is performing upgrades to all the hypervisors in the environment. Which of the following components of the hypervisors should be upgraded? (Choose two.)
A systems administrator is using a configuration management tool to perform maintenance tasks in a system. The tool is leveraging the target system's API to perform these maintenance tasks After a number of features and security updates are applied to the target system, the configuration management tool no longer works as expected. Which of the following is the MOST likely cause of the issue?
A cloud administrator is managing an organization's infrastructure in a public cloud. All servers are currently located in a single virtual network with a single firewall that all traffic must pass through. Per security requirements, production, QA, and development servers should not be able to communicate directly with each other. Which of the following should an administrator perform to comply with the security requirement?
A systems administrator is deploying a VM and would like to minimize storage utilization by ensuring the VM uses only the storage if needs. Which of the following will BEST achieve this goal?
A technician just received the lessons learned from some recent data that was lost due to an on-premises file-server crash. The action point is to change the backup strategy to minimize manual intervention. Which of the following is the BEST approach for the technician to implement?
A cloud administrator has created a new asynchronous workflow lo deploy VMs to the cloud in bulk. When the workflow is tested for a single VM, it completes successfully. However, if the workflow is used to create 50 VMs at once, the job fails. Which of the following is the MOST likely cause of the issue? (Choose two.)
A systems administrator is deploying a new virtualized environment. The setup is a three-server cluster with 12 VMs running on each server. While executing a vertical-scaling test of the vCPU on the VMs, the administrator gets an error. Which of the following issues is MOST likely occurring?
A systems administrator is responding to an outage in a cloud environment that was caused by a network-based flooding attack. Which of the following should the administrator configure to mitigate the attack?
An organization recently deployed a private cloud on a cluster of systems that delivers compute, network, and storage resources in a single hardware, managed by an intelligent software. Which of the following BEST describes this type of deployment?
A cloud administrator is responsible for managing a VDI environment that provides end users with access to limited applications. Which of the following should the administrator make changes to when a new application needs to be provided?
Audit and system logs are being forwarded to a syslog solution. An administrator observes that two application servers have not generated any logs for a period of three days, while others continue to send logs normally. Which of the following BEST explains what is occurring?
A company is deploying a public cloud solution for an existing application using lift and shift. The requirements for the applications are scalability and external access. Which of the following should the company implement? (Select TWO).
A systems administrator needs to migrate email services to the cloud model that requires the least amount of administrative effort. Which of the following should the administrator select?
A systems administrator has migrated a web application to the cloud with a synchronous uplink speed of 100Mbps. After the migration, the administrator receives reports of slow connectivity to the web application. The administrator logs into the firewall and notices the WAN port is transmitting at a constant 12.5MBps. Which of the following BEST explains the reason for the issue?
A company needs a solution to find content in images. Which of the following technologies, when used in conjunction with cloud services, would facilitate the BEST solution?
A technician needs to deploy two virtual machines in preparation for the configuration of a financial application next week. Which of the following cloud deployment models should the technician use?
A vendor is installing a new retail store management application for a customer. The application license ensures software costs are low when the application is not being used, but costs go up when use is higher.
Which of the following licensing models is MOST likely being used?
A company is doing a cloud-to-cloud migration to lower costs. A systems administrator has to plan the migration accordingly.
Which of the following considerations is MOST important for a successful, future-proof, and low-cost migration?
A cloud administrator has been using a custom VM deployment script. After three months of use, the script no longer joins the LDAP domain. The cloud administrator verifies the account has the correct permissions. Which of the following is the MOST likely cause of the failure?
A systems administrator is deploying a new cloud application and needs to provision cloud services with minimal effort. The administrator wants to reduce the tasks required for maintenance, such as OS patching, VM and volume provisioning, and autoscaling configurations. Which of the following would be the BEST option to deploy the new application?
A systems administrator swapped a failed hard drive on a server with a RAID 5 array. During the RAID resynchronization, a second hard drive failed.
Which of the following actions will make the server fully operational?
An administrator is securing a private cloud environment and wants to ensure only approved systems can connect to switches. Which of the following would be MOST useful to accomplish this task?
A cloud administrator wants to have a central repository for all the logs in the company’s private cloud. Which of the following should be implemented to BEST meet this requirement?
A systems administrator is analyzing a report of slow performance in a cloud application. This application is working behind a network load balancer with two VMs, and each VM has its own digital certificate configured. Currently, each VM is consuming 85% CPU on average. Due to cost restrictions, the administrator cannot scale vertically or horizontally in the environment. Which of the following actions should the administrator take to decrease the CPU utilization? (Choose two.)
An organization suffered a critical failure of its primary datacenter and made the decision to switch to the DR site. After one week of using the DR site, the primary datacenter is now ready to resume operations.
Which of the following is the MOST efficient way to bring the block storage in the primary datacenter up to date with the DR site?
A cloud administrator set up a link between the private and public cloud through a VPN tunnel. As part of the migration, a large set of files will be copied. Which of the following network ports are required from a security perspective?
A systems administrator is trying to establish an RDP session from a desktop to a server in the cloud. However, the connection appears to be refused even through the VM is responding to ICMP echo requests. Which of the following should the administrator check FIRST?
To save on licensing costs, the on-premises, IaaS-hosted databases need to be migrated to a public DBaaS solution. Which of the following would be the BEST technique?
A cloud solutions architect needs to determine the best strategy to deploy an application environment in production, given the following requirements:
No downtime
Instant switch to a new version using traffic control for all users
Which of the following deployment strategies would be the BEST solution?
A company wants to move its environment from on premises to the cloud without vendor lock-in. Which of the following would BEST meet this requirement?
A cloud administrator recently noticed that a number of files stored at a SaaS provider’s file-sharing service were deleted. As part of the root cause analysis, the administrator noticed the parent folder permissions were modified last week. The administrator then used a test user account and determined the permissions on the files allowed everyone to have write access.
Which of the following is the best step for the administrator to take NEXT?
A systems administrator needs to convert ten physical servers to virtual.
Which of the following would be the MOST efficient conversion method for the administrator to use?
A systems administrator is deploying a new storage array for backups. The array provides 1PB of raw disk space and uses 14TB nearline SAS drives. The solution must tolerate at least two failed drives in a single RAID set.
Which of the following RAID levels satisfies this requirement?
A company is utilizing a private cloud solution that is hosted within its datacenter. The company wants to launch a new business application, which requires the resources below:
The current private cloud has 30 vCPUs and 512GB RAM available. The company is looking for a quick solution to launch this application, with expected maximum sessions to be close to 24,000 at launch and an average of approximately 5,000 sessions.
Which of the following solutions would help the company accommodate the new workload in the SHORTEST amount of time and with the maximum financial benefits?
A developer is no longer able to access a public cloud API deployment, which was working ten minutes prior.
Which of the following is MOST likely the cause?
In an existing IaaS instance, it is required to deploy a single application that has different versions.
Which of the following should be recommended to meet this requirement?
A company wants to implement business continuity, and the cloud solution architect needs to design the correct solution.
Which of the following will provide the data to measure business continuity? (Choose two.)
An organization has two businesses that are developing different software products. They are using a single cloud provider with multiple IaaS instances. The organization identifies that the tracking of costs for each
business are inaccurate.
Which of the following is the BEST method for resolving this issue?
A systems administrator has migrated an internal application to a public cloud. The new web server is running under a TLS connection and has the same TLS certificate as the internal application that is deployed. However, the IT department reports that only internal users who are using new versions of the OSs are able to load the application home page.
Which of the following is the MOST likely cause of the issue?
A cloud administrator is designing a multiregion network within an IaaS provider. The business requirements for configuring the network are as follows:
Use private networking in and between the multisites for data replication.
Use low latency to avoid performance issues.
Which of the following solutions should the network administrator use within the IaaS provider to connect multiregions?
An organization is required to set a custom registry key on the guest operating system.
Which of the following should the organization implement to facilitate this requirement?
An organization has the following requirements that need to be met when implementing cloud services:
SSO to cloud infrastructure
On-premises directory service
RBAC for IT staff
Which of the following cloud models would meet these requirements?
Which of the following cloud deployment models allows a company to have full control over its IT infrastructure?
A cloud administrator checked out the deployment scripts used to deploy the sandbox environment to a public cloud provider. The administrator modified the script to add an application load balancer in front of the web- based front-end application. The administrator next used the script to recreate a new sandbox environment successfully, and the application was then using the new load balancer.
The following week, a new update was required to add more front-end servers to the sandbox environment. A second administrator made the necessary changes and checked out the deployment scripts. The second administrator then ran the script, but the application load balancer was missing from the new deployment.
Which of the following is the MOST likely reason for this issue?
A company just successfully completed a DR test and is ready to shut down its DR site and resume normal operations.
Which of the following actions should the cloud administrator take FIRST?
A cloud administrator is switching hosting companies and using the same script that was previously used to deploy VMs in the new cloud. The script is returning errors that the command was not found.
Which of the following is the MOST likely cause of the script failure?
An update is being deployed to a web application, and a systems administrator notices the cloud SQL database has stopped running. The VM is responding to pings, and there were not any configuration changes scheduled for the VM. Which of the following should the administrator check NEXT?
A cloud administrator is reviewing the authentication and authorization mechanism implemented within the cloud environment. Upon review, the administrator discovers the sales group is part of the finance group, and the sales team members can access the financial application. Single sign-on is also implemented, which makes access much easier.
Which of the following access control rules should be changed?
An IaaS application has a two-hour RTO and a four-hour RPO. The application takes one hour to back up its data or restore from a local backup file. A systems administrator is tasked with configuring the backup policy.
Which of the following should the administrator configure to achieve the application requirements with the LEAST cost?
A cloud architect wants to minimize the risk of having systems administrators in an IaaS compute instance perform application code changes. The development group should be the only group allowed to modify files in the directory.
Which of the following will accomplish the desired objective?
A systems administrator is configuring a storage array.
Which of the following should the administrator configure to set up mirroring on this array?
A cloud administrator needs to control the connections between a group of web servers and database servers as part of the financial application security review. Which of the following would be the BEST way to achieve this objective?
An organization has a public-facing API that is hosted on a cloud provider. The API performs slowly at times. Which of the following technologies should the cloud administrator apply to provide speed acceleration and a secure connection?
A company wants to utilize its private cloud for a new application. The private cloud resources can meet 75% of the application's resource requirements. Which of the following
scaling techniques can the cloud administrator implement to accommodate 100% of the application's requirements?
A cloud administrator is troubleshooting a highly available web application running within three containers behind a Layer 7 load balancer with a WAF inspecting all traffic. The application frequently asks the users to log in again even when the session timeout has not been reached. Which of the following should the cloud administrator configure to solve this issue?
A company is migrating workloads from on premises to the cloud and would like to establish a connection between the entire data center and the cloud environment. Which of the following VPN configurations would accomplish this task?
A systems administrator received an email from a cloud provider stating that storage is 80% full on the volume that stores VDI desktops. Which of the following is the MOST efficient way to mitigate the situation?
Which of the following should a cloud architect consider for a containerized cluster in a cloud environment?
A web application has been configured to use autoscaling for provisioning and deprovisioning more VMs according to the workload. The systems administrator deployed a new CI/CD tool to automate new releases of the web application. During the night, a script was deployed and configured to be executed by the VMs during bootstrapping. Now. the autoscaling configuration is creating a new VM ever\ five minutes. Which of the following actions will MOS I like y resolve the issue?
A technician deployed a VM with NL-SAS storage to host a critical application. Two weeks later, users have begun to report high application latency. Which of the following is the BEST action to correct the latency issue?
A systems administrator is troubleshooting performance issues with a Windows VDI environment. Users have reported that VDI performance is very slow at the start of the workday, but the performance is fine during the rest of the day. Which of the following is the MOST likely cause of the issue? (Select TWO).
A systems administrator needs to implement a service to protect a web application from external attacks. The administrator must have session-based granular control of all HTTP traffic. Which of the following should the administrator configure?
A company is performing a DR drill and is looking to validate its documentation. Which of the following metrics will determine the service recovery duration?
A systems administrator is concerned about having two virtual database servers on the same host. Which of the following should be configured?
A systems administrator is working on the backup schedule for a critical business application that is running in a private cloud. Which of the following would help the administrator schedule the frequency of the backup job?
A security audit related to confidentiality controls found the following transactions occurring in the system:
GET http://gateway.securetransaction.com/privileged/api/v1/changeResource?id=123 &user=277
Which of the following solutions will solve the audit finding?
A systems administrator deployed a new application release to the green stack of a blue-green infrastructure model and made the green stack primary. Immediately afterward, users began reporting application issues. The systems administrator must take action to bring the service online as quickly as possible. Which of the following is the FASTEST way to restore the service?
A web-application company recently released some new marketing promotions without notifying the IT staff. The systems administrator has since been noticing twice the normal traffic consumption every two hours for the last three hours in the container environment. Which of the following should the company implement to accommodate the new traffic?
A systems administrator is diagnosing performance issues on a web application. The web application sends thousands of extremely complex SQL queries to a database server, which has trouble retrieving the information in time. The administrator checks the database server and notes the following resource utilization:
CPU: 64%
RAM: 97%
Network throughput: 384,100Kbps.
Disk throughput: 382,700Kbps
The administrator also looks at the storage for the database server and notices it is consistently near its OPS limit. Which of the following will BEST resolve these performance issues?
A cloud administrator needs to establish a secure connection between two different locations. Which of the following is the BEST option to implement the secure connection?
A cloud administrator needs to verify domain ownership with a third party. The third party has provided a secret that must be added to the DNS server. Which of the following DNS records does the administrator need to update to include the secret?
A cloud engineer is deploying a server in a cloud platform. The engineer reviews a security scan report. Which of the following recommended services should be disabled? (Select TWO).
A cloud administrator deployed new hosts in a private cloud. After a few months elapsed, some of the hypervisor features did not seem to be working. Which of the following was MOST likely causing the issue?
A systems administrator is implementing a new version of a company's primary human-resources application. An upgrade will be performed on the production server, as there is no development environment. The administrator needs to have a
plan in case something goes wrong with the upgrade. Which of the following will work best to ensure a quick rollback in case an issue arises?
A non-critical file on a database server was deleted and needs to be recovered. A cloud administrator must use the least disruptive restoration process to retrieve the file, as the database server cannot be stopped during the business day. Which of the following restoration methods would best accomplish this goal?
A cloud administrator receives an email stating the following:
"Clients are receiving emails from our web application with non-encrypted links."
The administrator notices that links generated from the web application are opening in http://. Which of the following should be configured to redirect the traffic to https://?
Which of the following provides groups of compute units that can horizontally scale according to a workload?
A systems administrator is building a standardized OS template for the deployment of a web service. The image is intended for various autoscaling groups. Which of the following should be included in the image as best practice?
A company is using a hybrid cloud environment. The private cloud is hosting the business applications, and the cloud services are being used to replicate for availability purposes.
The cloud services are also being used to accommodate the additional resource requirements to provide continued services. Which of the following scalability models is the company utilizing?
A database analyst reports it takes two hours to perform a scheduled job after onboarding 10,000 new users to the system. The analyst made no changes to the scheduled job before or after onboarding the users. The database is hosted in an IaaS instance on a cloud provider. Which of the following should the cloud administrator evaluate to troubleshoot the performance of the job?
A system administrator is migrating a bare-metal server to the cloud. Which of the following types of migration should the systems administrator perform to accomplish this task?
A systems administrator has finished installing monthly updates to servers in a cloud environment. The administrator notices certain portions of the playbooks are no longer functioning. Executing the playbook commands manually on a server does not work as well. There are no other reports of issues.
Which of the following is the MOST likely cause of this issue?
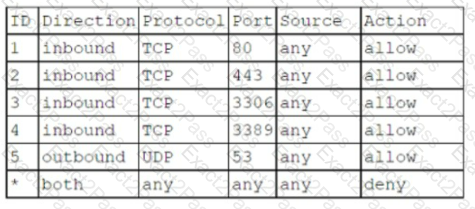
A cloud security analyst needs to ensure the web servers in the public subnet allow only secure communications and must remediate any possible issue. The stateful configuration for the public web servers is as follows:
Which of the following actions should the analyst take to accomplish the objective?
Users are experiencing slow response times from an intranet website that is hosted on a cloud platform. There is a site-to-site VPN connection to the cloud provider over a link of 100Mbps.
Which of the following solutions will resolve the issue the FASTEST?
A systems administrator is deploying a solution that includes multiple network I/O-intensive VMs. The solution design requires that vNICs of the VMs provide low-latency, near-native performance of a physical NIC and data protection between the VMs. Which of the following would BEST satisfy these requirements?
A cloud administrator is reviewing a new application implementation document. The administrator needs to make sure all the known bugs and fixes are applied, and unwanted ports and services are disabled.
Which of the following techniques would BEST help the administrator assess these business requirements?
A systems administrator needs to configure SSO authentication in a hybrid cloud environment.
Which of the following is the BEST technique to use?
An organization is hosting a cloud-based web server infrastructure that provides web-hosting solutions. Sudden continuous bursts of traffic have caused the web servers to saturate CPU and network utilizations.
Which of the following should be implemented to prevent such disruptive traffic from reaching the web servers?
A systems administrator is creating a playbook to run tasks against a server on a set schedule.
Which of the following authentication techniques should the systems administrator use within the playbook?
A media company has made the decision to migrate a physical, internal file server to the cloud and use a web- based interface to access and manage the files. The users must be able to use their current corporate logins.
Which of the following is the MOST efficient way to achieve this goal?
Company A has acquired Company B and is in the process of integrating their cloud resources. Company B needs access to Company A’s cloud resources while retaining its IAM solution.
Which of the following should be implemented?
A systems administrator is troubleshooting issues with network slowness. Traffic analysis shows that uplink bandwidth on the core switch is often sustained at 125Mbps due to a
combination of production traffic from other sources. Which of the following would BEST resolve the issue?
A company is using a method of tests and upgrades in which a small set of end users are exposed to new services before the majority of other users. Which of the following deployment methods is being used?
After initial stress testing showed that a platform performed well with the specification of a single 32 vCPU node, which of the following will provide the desired service with the LOWEST cost and downtime?
A systems administrator needs to modify the replication factors of an automated application container from 3 to 5. Which of the following file types should the systems administrator modify on the master controller?
During a security incident, an laaS compute instance is detected to send traffic to a host related to cryptocurrency mining. The security analyst handling the incident determines the scope of the incident is limited to that particular instance. Which of the following should the security analyst do NEXT?
A cloud administrator is configuring several security appliances hosted in the private laaS environment to forward the logs to a central log aggregation solution using syslog. Which of the following firewall rules should the administrator add to allow the web servers to connect to the central log collector?
A cloud solutions architect has an environment that must only be accessed during work hours. Which of the following processes should be automated to BEST reduce cost?
A cloud administrator created four VLANs to autoscale the container environment. Two of the VLANs are on premises, while two VLANs are on a public cloud provider with a direct link between them. Firewalls are between the links with an additional subnet for communication, which is 192.168.5.0/24.
The on-premises gateways are:
192.168.1.1/24
192.168.2.1/24
The cloud gateways are:
192.168.3.1/24
192.168.4.1/24
The orchestrator is unable to communicate with the cloud subnets. Which Of the following should the administrator do to resolve the issue?
A cloud engineer is responsible for managing two cloud environments from different MSPs. The security department would like to inspect all traffic from the two cloud environments.
Which of the following network topology solutions should the cloud engineer implement to reduce long-term maintenance?
A systems administrator recently deployed a VDI solution in a cloud environment; however, users are now experiencing poor rendering performance when trying to display 3-D content on their virtual desktops, especially at peak times.
Which of the following actions will MOST likely solve this issue?
A company wants to check its infrastructure and application for security issues regularly. Which of the following should the company implement?
Which of the following enables CSPs to offer unlimited capacity to customers?
An integration application that communicates between different application and database servers is currently hosted on a physical machine. A P2V migration needs to be done to reduce the hardware footprint. Which of the following should be considered to maintain the same level of network throughput and latency in the virtual server?
A systems administrator is reviewing the logs from a company's IDS and notices a large amount of outgoing traffic from a particular server. The administrator then runs a scan on the server, which detects malware that cannot be removed. Which of the following should the administrator do first?
A cloud engineer receives an alert that a newly provisioned server is running a non-supported Linux version. The automation scripts are performing as expected on the server. Which of the following should the engineer check first?
A company's marketing department is running a rendering application on virtual desktops. Currently, the application runs slowly, and it takes a long time to refresh the screen. The virtualization administrator is tasked with resolving this issue. Which of the following is the BEST solution?
An application deployment team has observed delays in deployments and has asked the cloud administrator to evaluate the issue. Below is the result of a latency test that was conducted by the cloud administrator from offices located in the following regions:
• Asia-Pacific (APAC)
• Europe, the Middle East, and Africa (EMEA)
• Americas
Tests were conducted from each location, and the results are shown below:
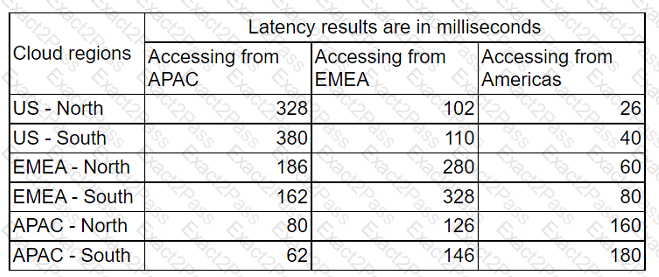
Which of the following locations needs to be investigated further?
A systems administrator needs to provide information for a capacity-planning document. Which of the following is the most relevant baseline and capacity information?
A corporation is evaluating an offer from a CSP to take advantage of volume discounts on a shared platform. The finance department is concerned about cost allocation transparency, as the current structure splits projects into dedicated billing accounts. Which of the following can be used to address this concern?
An organization is implementing a new requirement to facilitate users with faster downloads of corporate application content. At the same time, the organization is also expanding cloud regions.
Which of the following would be suitable to optimize the network for this requirement?
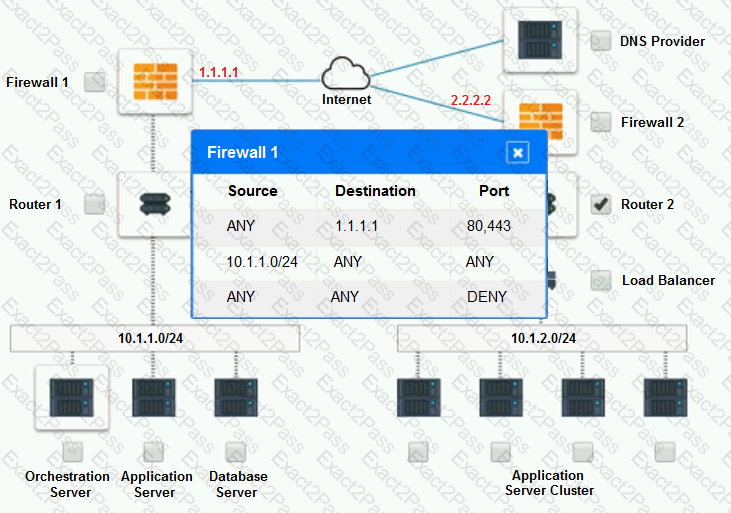
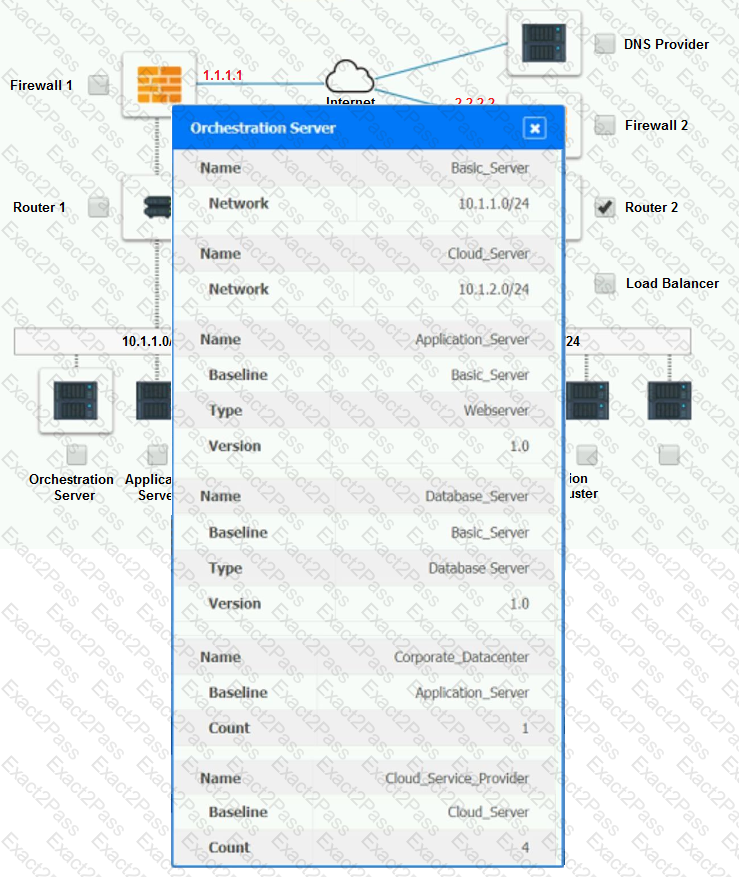
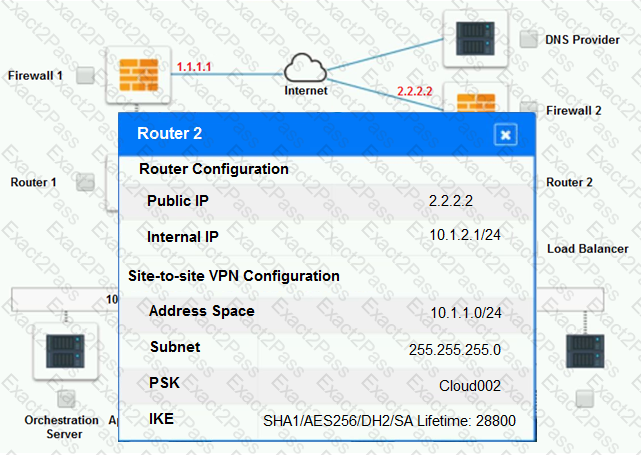
A company has decided to scale its e-commerce application from its corporate datacenter to a commercial cloud provider to meet an anticipated increase in demand during an upcoming holiday.
The majority of the application load takes place on the application server under normal conditions. For this reason, the company decides to deploy additional application servers into a commercial cloud provider using the on-premises orchestration engine that installs and configures common software and network configurations.
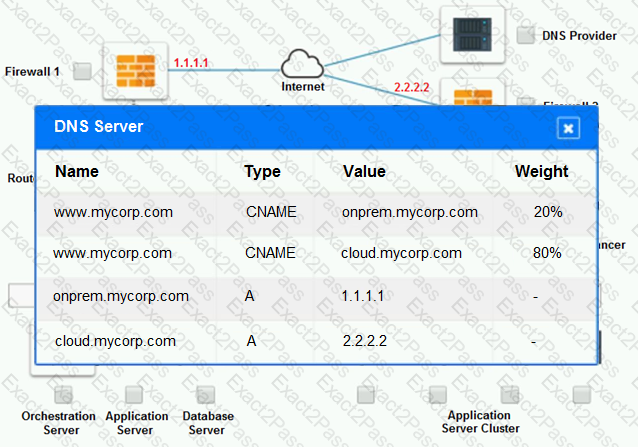
The remote computing environment is connected to the on-premises datacenter via a site-to-site IPSec tunnel. The external DNS provider has been configured to use weighted round-robin routing to load balance connections from the Internet.
During testing, the company discovers that only 20% of connections completed successfully.
INSTRUCTIONS
Review the network architecture and supporting documents and fulfill these requirements:
Part 1:
 Analyze the configuration of the following components: DNS, Firewall 1, Firewall 2, Router 1, Router 2, VPN and Orchestrator Server.
Analyze the configuration of the following components: DNS, Firewall 1, Firewall 2, Router 1, Router 2, VPN and Orchestrator Server.
 Identify the problematic device(s).
Identify the problematic device(s).
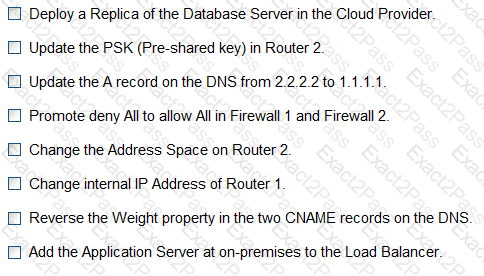
Part 2:
 Identify the correct options to provide adequate configuration for hybrid cloud architecture.
Identify the correct options to provide adequate configuration for hybrid cloud architecture.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Part 1:
Cloud Hybrid Network Diagram
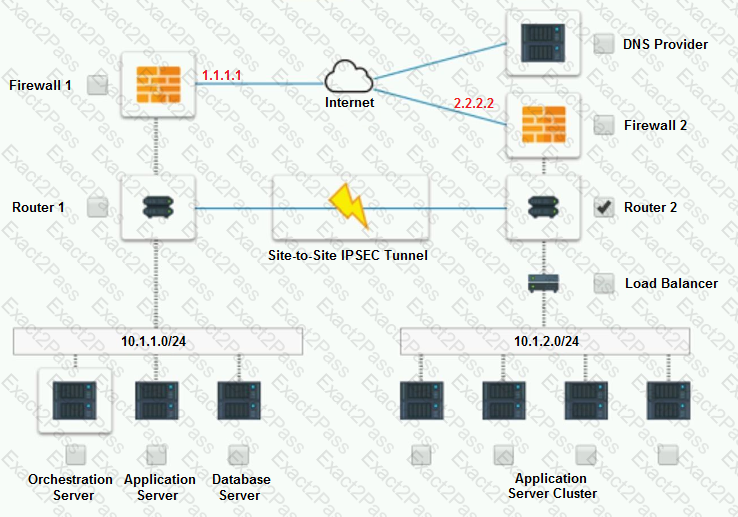
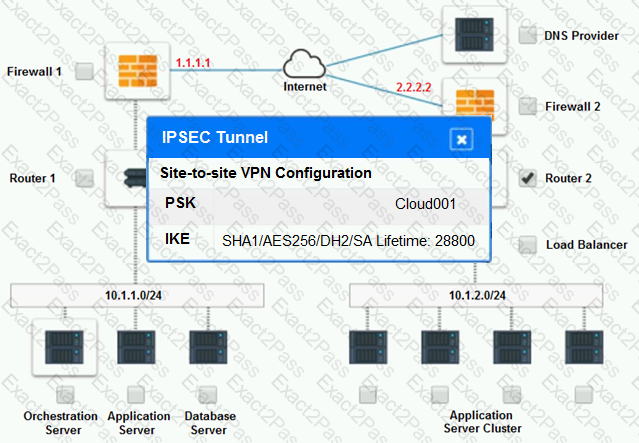
Part 2:
Only select a maximum of TWO options from the multiple choice question
An organization requires the following to be achieved between the finance and marketing departments:
Allow HTTPS/HTTP.
Disable FTP and SMB traffic.
Which of the following is the MOST suitable method to meet the requirements?
A company has applications that need to remain available in the event of the data center being unavailable. The company's cloud architect needs to find a solution to maintain business continuity. Which of following should the company implement?
A systems administrator is planning the storage requirements for a two-disk mirror of a server OS disk partition. Which of the following is the amount of disk space available in the mirrored volume?
A systems administrator has verified that a physical switchport that is connected to a virtualization host is using all available bandwidth. Which of the following would best address this issue?
A cloud administrator has deployed a website and needs to improve the site security to meet requirements. The website architecture is designed to have a DBaaS in the back end and autoscaling instances in the front end using a load balancer to distribute the request. Which of the following will the cloud administrator most likely use?
After an infrastructure-as-code cloud migration to an laaS environment, the cloud engineer discovers that configurations on DB servers have drifted from the corporate standard baselines. Which of the following should the cloud engineer do to best ensure configurations are restored to the baselines?
An organization will be deploying a web application in a public cloud with two web servers, two database servers, and a load balancer that is accessible over a single public IP.
Taking into account the gateway for this subnet and the potential to add two more web servers, which of the following will meet the minimum IP requirement?
A cloud administrator is choosing a backup schedule for a new application platform that creates many small files. The backup process impacts the performance of the application, and backup times should be minimized during weekdays. Which of the following backup types best meets the weekday requirements?
A cloud engineer is troubleshooting RSA key-based authentication from a local computer to a cloud-based server, which is running SSH service on a default port. The following file
permissions are set on the authorized keys file:
-rw-rw-rw-1 ubuntu ubuntu 391 Mar S 01:36 authorized _ keys
Which Of the following security practices are the required actions the engineer Should take to gain access to the server? (Select TWO).
A cloud security analyst needs to ensure the web servers in the public subnet allow only secure communications and must remediate any possible issue. The stateful configuration for the public web servers is as follows:
Which Of the following actions Should the analyst take to accomplish the Objective?
A DevOps engineer needs to provide sensitive information to applications running as containers. The sensitive information will be updated based on the environment in which the container will be deployed. Which of the following should the engineer leverage to ensure the data remains protected?
A systems administrator is deploying a new version of a website. The website is deployed in the cloud using a VM cluster. The administrator must then deploy the new version into one VM first. After a period of time, if there are no issues detected, a second VM will be updated. This process must continue until all the VMS are updated. Which of the following upgrade methods is being implemented?
Different healthcare organizations have agreed to collaborate and build a cloud infrastructure that should minimize compliance costs and provide a high degree of security and privacy, as per regulatory requirements. This is an example of a:
A company has a large environment with multiple VPCs across three regions in a public cloud. The company is concerned about connectivity within the regions. Which of the following should the cloud administrator implement?
A company is using laaS services from two different providers: one for its primary site, and the other for a secondary site. The primary site is completely inaccessible, and the management team has decided to run through the BCP procedures. Which of the following will provide the complete asset information?
A systems administrator is diagnosing performance issues on a web application. The web application sends thousands of extremely complex SQL queries to a database server, which has trouble retrieving the information in time. The administrator checks the database server and notes the following resource utilization:
CPU: 64%
RAM: 97%
Network throughput: 384/1000 Kbps
Disk throughput: 382,700 Kbps
The administrator also notices that the storage for the database server is consistently near its IOPS limit. Which of the following will best resolve these performance issues?
A VDI provider suspects users are installing prohibited software on the instances. Which of the following must be implemented to prevent the issue?