Last Update 19 hours ago Total Questions : 196
The HCIP-Security-CSSN V3.0 content is now fully updated, with all current exam questions added 19 hours ago. Deciding to include H12-722_V3.0 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our H12-722_V3.0 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these H12-722_V3.0 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any HCIP-Security-CSSN V3.0 practice test comfortably within the allotted time.
Based on the anti-virus gateway of streaming scan, which of the following descriptions is wrong?
When you suspect that the company ' s network has been attacked by hackers, you have carried out a technical investigation. Which of the following options does not belong to the behavior that occurred in the early stage of the attack?
Huawei USG6000 products can scan and process certain file transfer protocols for viruses, but which of the following protocols is not included?
Which of the following files can the sandbox detect? (multiple choice)
Which patches does Policy Center support to management?(Choose 3 answers)
Which of the following descriptions about viruses and Trojans are correct? (multiple choices)
The application behavior control configuration file takes effect immediately after being referenced, without configuration submission.
The results of the RBL black and white list query on the firewall are as follows:
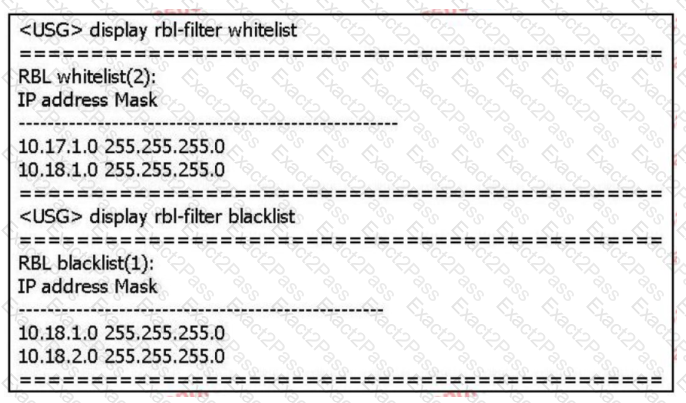
Based on the above information only, which of the following statements is correct? (multiple choice)
Viruses can damage computer systems. v Change and damage business data: spyware collects, uses, and disperses sensitive information of corporate employees.
These malicious pastoral software seriously disturb the normal business of the enterprise. Desktop anti-disease software can solve the problem of central virus and indirect software from the overall situation.
Configure the following commands on the Huawei firewall:
[USG] interface G0/0/1
[USG] ip urpf loose allow-defult-route acl 3000
Which of the following options are correct? (multiple choice)

