Last Update 9 hours ago Total Questions : 367
The HCIP-Security (Fast track) V1.0 content is now fully updated, with all current exam questions added 9 hours ago. Deciding to include H12-724 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our H12-724 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these H12-724 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any HCIP-Security (Fast track) V1.0 practice test comfortably within the allotted time.
In the Agile Controller-Campus admission control technology framework, regarding the description of RADIUS, which of the following options is correct?
In the Policy Center strategy configuration, how many violations rating of definition are there?
The following figure is a schematic diagram of the detection file of the firewall and the sandbox system linkage.
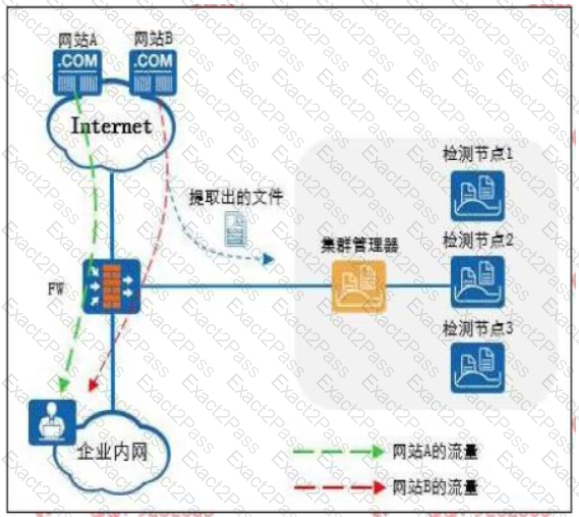
The Web reputation function is enabled on the firewall, and website A is set as a trusted website and website B is set as a suspicious website.
Which of the following statements is correct
Which of the following options are common behavioral characteristics of viruses? (multiple choices)
Regarding worms and viruses, which of the following statements is correct?
Regarding intrusion detection I defense equipment, which of the following statements are correct? (multiple choice)
For hardware SACC Access control, if the terminal does not pass the authentication, it can access the resources of the post-authentication domain. This phenomenon may be caused by the following reasons? (Multiple choice)
Which of the following statement is correct about Policy Center system client function?
BY00 The products and textiles provided by the history solution program cover the entire terminal network\Application and management and other fields/include: Serialization BC Equipment, paperless network system network access support, VPN Gateway, terminal security customer ladder software, authentication system, mobile device management(MDN),move eSpace UC.
When a virus is detected in an email, which of the following is not the corresponding action for detection?

