Last Update 4 hours ago Total Questions : 62
The CIW v5 Security Essentials content is now fully updated, with all current exam questions added 4 hours ago. Deciding to include 1D0-571 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 1D0-571 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 1D0-571 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any CIW v5 Security Essentials practice test comfortably within the allotted time.
Your organization has made a particularly unpopular policy decision. Your supervisor fears that a series of attacks may occur as a result. You have been assigned to increase automated auditing on a server. When fulfilling this request, which of the following resources should you audit the most aggressively?
You want to create a quick solution that allows you to obtain real-time login information for the administrative account on an LDAP server that you feel may become a target. Which of the following will accomplish this goal?
Consider the following diagram:
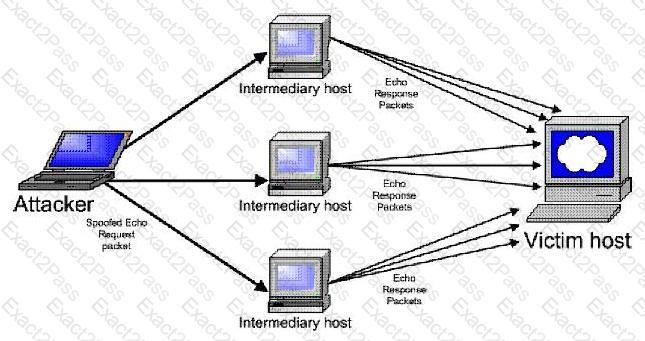
Which type of attack is occurring?
Consider the following diagram involving two firewall-protected networks:

Which of the following is necessary for each of the firewalls to allow private IP addresses to be passed on to the Internet?
Which of the following organizations provides regular updates concerning security breaches and issues?
A disgruntled employee has discovered that the company Web server is not protected against a particular buffer overflow vulnerability. The disgruntled employee has created an application to take advantage of this vulnerability and secretly obtain sensitive data from the Web server ' s hard disk. This application sends a set of packets to the Web server that causes it to present an unauthenticated terminal with root privileges. What is the name for this particular type of attack?
Which of the following details should be included in documentation of an attack?
You have determined that the company Web server has several vulnerabilities, including a buffer overflow that has resulted in an attack. The Web server uses PHP and has direct connections to an Oracle database server. It also uses many CGI scripts. Which of the following is the most effective way to respond to this attack?

