Last Update 23 hours ago Total Questions : 124
The MySQL 5.7 Database Administrator content is now fully updated, with all current exam questions added 23 hours ago. Deciding to include 1z0-888 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 1z0-888 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 1z0-888 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any MySQL 5.7 Database Administrator practice test comfortably within the allotted time.
Which statement is correct about how InnoDB storage engine uses disk space?
The MySQL installation includes the mysql_config_editor utility for managing login paths stored in a .mylogin.cnf file.
Which two are true about the login path feature? (Choose two.)
SQL injection is a common security threat.
Which two methods would help protect against this risk?
Which two statements are true regarding MySQL security? (Choose two.)
Which two options describe how MySQL Server allocates memory? (Choose two.)
What is the order of tables shown in an EXPLAIN output?
You have a MySQL instance with the following variables in the /etc/my.cnf file:
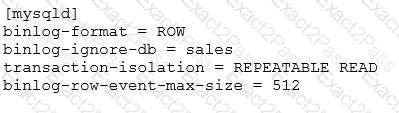
You issue these statements:
USE prices;
UPDATE sales.january SET amount=amount+1000;
An hour after excluding the statements, you realize that you made a mistake and you want to go to the binary log and look at the statements again.
Which statement is true? (Choose two.)
You inherited a busy InnoDB OLTP Instance with 100 schemas and 100 active users per schema.
Total dataset size is 200G with an average schema size of 2G.
The data is transient and is not backed up and can be repopulated easily.
Performance and responsiveness of the DB is paramount.
The query pattern for the DB instance is split 90/10 read/write.
DB host is dedicated server with 256G RAM and 64 cores.
One of your colleagues made some recent changes to the system and users are now complaining of performance impacts.
Which four configuration file edits might your colleague have performed to cause the negative DB performance? (Choose four.)
A crucial database, ‘db_prod’, just disappeared from your production MySQL instance.
In reviewing the available MySQL logs (General, Audit, or Slow) and your own application-level logs, you identified this command from a customer facing application:
SELECT id FROM users WHERE login=’payback!’;DROP DATABASE db_prod;’
Which three methods could have been used to prevent this SQL injection attack from happening? (Choose three.)
Consider the CHECK TABLE command.
In which two situations should this command be used? (Choose two.)

