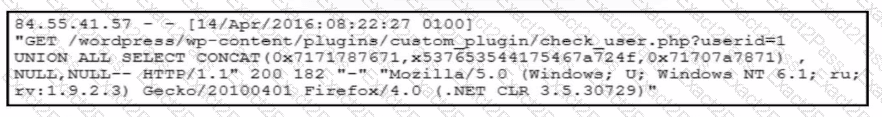
The correct answer is Exploit public-facing application . The log excerpt in the exhibit clearly shows a malicious HTTP GET request targeting a WordPress plugin PHP file with a crafted SQL injection payload :
UNION ALL SELECT CONCAT(...)
This syntax is a classic indicator of SQL injection , a well-documented attack technique used to exploit insufficient input validation in web applications. According to the MITRE ATT & CK framework, this behavior maps to the Initial Access tactic (TA0001) and the technique Exploit Public-Facing Application (T1190) . The attacker is directly interacting with a publicly accessible web service and abusing a vulnerability in the application code to gain unauthorized access.
From a threat hunting and forensic standpoint, this is a textbook example of how attackers commonly achieve initial access to web servers. The attacker did not authenticate via remote services (such as SSH or RDP), nor did they rely on user interaction (as in a drive-by compromise). Instead, they sent a specially crafted request to a vulnerable endpoint exposed to the internet. This makes option B incorrect because External Remote Services requires legitimate service access mechanisms. Option C is also incorrect because Command and Scripting Interpreter is typically used after initial access, once code execution is already achieved. Option D does not apply because there is no evidence of malicious content being delivered to end users.
The forensic team’s actions—isolating the server, cloning the disk, and analyzing logs—are standard post-incident procedures to reconstruct the attack chain. Web server access logs are especially valuable in these cases, as they often reveal malicious payloads, attacker IP addresses, targeted endpoints, and timestamps.
For defenders and threat hunters, this scenario reinforces the importance of monitoring web logs for anomalous query strings, enforcing secure coding practices, conducting regular vulnerability scans, and promptly patching third-party plugins. Public-facing applications remain one of the most exploited initial access vectors , making this technique a critical focus area in modern threat hunting programs.