Last Update 9 hours ago Total Questions : 60
The Conducting Threat Hunting and Defending using Cisco Technologies for Cybersecurity 300-220 CBRTHD content is now fully updated, with all current exam questions added 9 hours ago. Deciding to include 300-220 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 300-220 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 300-220 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Conducting Threat Hunting and Defending using Cisco Technologies for Cybersecurity 300-220 CBRTHD practice test comfortably within the allotted time.
The CISO must improve the threat-hunting strategy to strengthen the organization's security posture and better prepare against sophisticated threats. Which aspect of the Threat Hunting Maturity Model can significantly enhance an organization's ability to address challenges outlined in the Pyramid of Pain?
A threat hunter is asked to model how an attacker could abuse cloud identity misconfigurations to escalate privileges without exploiting software vulnerabilities. Which modeling approach BEST supports this analysis?
A structured threat hunt using Cisco Secure Network Analytics confirms abnormal internal SMB traffic consistent with lateral movement. Which action should occur NEXT to improve organizational security posture?
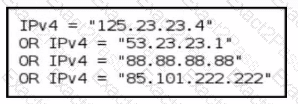
Refer to the exhibit.
A threat-hunting team makes an EDR query to detect possible C2 outbound communication across all endpoints. Which level of the Pyramid of Pain is being used?
A mature SOC notices that several incidents over the past year involved attackers abusing legitimate administrative tools rather than deploying custom malware. Leadership asks the threat hunting team to improve detection coverage in a way that increases attacker cost rather than relying on easily replaceable indicators. Which detection strategy best aligns with this objective?
A security operations team is transitioning from alert-driven investigations to a mature threat hunting program. The team wants to focus on detecting adversaries who intentionally evade signature-based tools and traditional SIEM alerts by using legitimate credentials and native system utilities. Which hunting focus best supports this objective?
A threat hunter uses Cisco Secure Network Analytics (Stealthwatch) to identify potential command-and-control traffic. Which characteristic MOST strongly indicates beaconing behavior?

