Last Update 14 hours ago Total Questions : 736
The Certified Professional Ethical Hacker (CPEH) content is now fully updated, with all current exam questions added 14 hours ago. Deciding to include CPEH-001 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our CPEH-001 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these CPEH-001 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Certified Professional Ethical Hacker (CPEH) practice test comfortably within the allotted time.
When comparing the testing methodologies of Open Web Application Security Project (OWASP) and Open Source Security Testing Methodology Manual (OSSTMM) the main difference is
The " white box testing " methodology enforces what kind of restriction?
Cryptography is the practice and study of techniques for secure communication in the presence of third parties (called adversaries.) More generally, it is about constructing and analyzing protocols that overcome the influence of adversaries and that are related to various aspects in information security such as data confidentiality, data integrity, authentication, and non-repudiation. Modern cryptography intersects the disciplines of mathematics, computer science, and electrical engineering. Applications of cryptography include ATM cards, computer passwords, and electronic commerce.
Basic example to understand how cryptography works is given below:
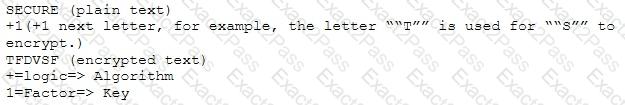
Which of the following choices is true about cryptography?
The establishment of a TCP connection involves a negotiation called 3 way handshake. What type of message sends the client to the server in order to begin this negotiation?
In Risk Management, how is the term " likelihood " related to the concept of " threat? "
A network administrator discovers several unknown files in the root directory of his Linux FTP server. One of the files is a tarball, two are shell script files, and the third is a binary file is named " nc. " The FTP server ' s access logs show that the anonymous user account logged in to the server, uploaded the files, and extracted the contents of the tarball and ran the script using a function provided by the FTP server ' s software. The ps command shows that the nc file is running as process, and the netstat command shows the nc process is listening on a network port.
What kind of vulnerability must be present to make this remote attack possible?
Which of the following is a common Service Oriented Architecture (SOA) vulnerability?
Which element of Public Key Infrastructure (PKI) verifies the applicant?
Which type of security document is written with specific step-by-step details?
A penetration test was done at a company. After the test, a report was written and given to the company ' s IT authorities. A section from the report is shown below:
According to the section from the report, which of the following choice is true?
Which of the following tools can be used for passive OS fingerprinting?
Which of the following programming languages is most susceptible to buffer overflow attacks, due to its lack of a built-in-bounds checking mechanism?
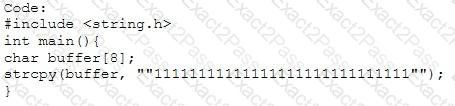
Output:
Segmentation fault
What network security concept requires multiple layers of security controls to be placed throughout an IT infrastructure, which improves the security posture of an organization to defend against malicious attacks or potential vulnerabilities?
How does a denial-of-service attack work?
Yancey is a network security administrator for a large electric company. This company provides power for over 100, 000 people in Las Vegas. Yancey has worked for his company for over 15 years and has become very successful. One day, Yancey comes in to work and finds out that the company will be downsizing and he will be out of a job in two weeks. Yancey is very angry and decides to place logic bombs, viruses, Trojans, and backdoors all over the network to take down the company once he has left. Yancey does not care if his actions land him in jail for 30 or more years, he just wants the company to pay for what they are doing to him.
What would Yancey be considered?

