Last Update 1 day ago Total Questions : 20
The Dell Security Foundations Achievement content is now fully updated, with all current exam questions added 1 day ago. Deciding to include D-SF-A-24 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our D-SF-A-24 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these D-SF-A-24 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Dell Security Foundations Achievement practice test comfortably within the allotted time.
A R.T.I.E.'s business is forecast to grow tremendously in the next year, the organization will not only need to hire new employees but also requires contracting with third-party vendors to continue seamless operations. A .R.T.I.E. uses a VPN to support its employees on the corporate network, but the organization is facing a security challenge in supporting the third-party business vendors.
To better meet A .R.T.I.E.'s security needs, the cybersecurity team suggested adopting a Zero Trust architecture (ZTA). The main aim was to move defenses from static, network-based perimeters to focus on users, assets, and resources. Zero Trust continuously ensures that a user is authentic and the request for resources is also valid. ZTA also helps to secure the attack surface while supporting vendor access.
What is the main challenge that ZTA addresses?
Dell Services team cannot eliminate all risks, but they can continually evaluate the resilience and preparedness of A .R.T.I.E. by using the National Institute of Standards and Technology Cybersecurity Framework (NIST CSF).
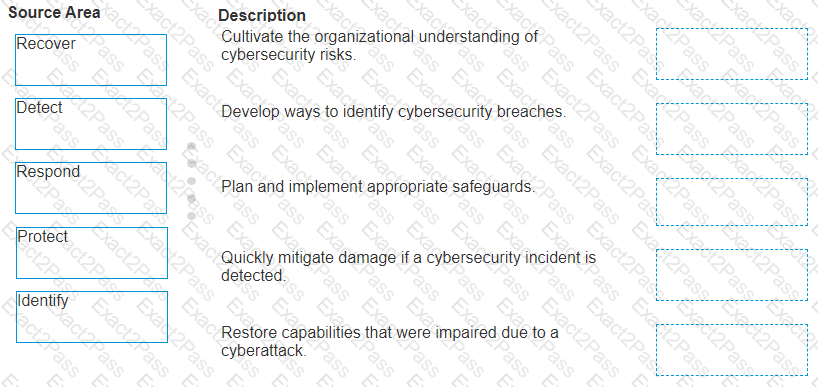
Match the core NIST CSF component functions with the description that the Dell Services team would have recommended to A .R.T.I.E.
During the analysis, the threat intelligence team disclosed that attackers not only encrypted files, but also attempted to encrypt backups and shared, networked, and cloud drives.
Which type of ransomware is used for this attack?

