Last Update 21 hours ago Total Questions : 73
The Trend Micro Certified Professional for Deep Security Exam content is now fully updated, with all current exam questions added 21 hours ago. Deciding to include Deep-Security-Professional practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our Deep-Security-Professional exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these Deep-Security-Professional sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Trend Micro Certified Professional for Deep Security Exam practice test comfortably within the allotted time.
Your organization would like to implement a mechanism to alert administrators when files on a protected servers are modified or tampered with. Which Deep Security Protection Module should you enable to provide this functionality?
Which of the following statements is true regarding Deep Security Relays?
Recommendation scans can detect applications and/or vulnerabilities on servers on the network. Which of the following Protection Modules make use of Recommendation scans?
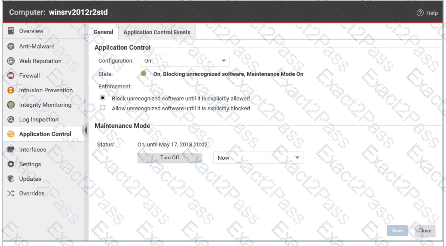
Based on the following exhibit, what behavior would you expect for the Application Control Protection Module?
Which of the following is not an operation that is performed when network traffic is intercepted by the network driver on the Deep Security Agent?
How is scan caching used in agentless implementations of Deep Security?
As the administrator in a multi-tenant environment, you would like to monitor the usage of security services by tenants? Which of the following are valid methods for monitoring the usage of the system by the tenants?

