Last Update 16 hours ago Total Questions : 150
The ECCouncil Computer Hacking Forensic Investigator content is now fully updated, with all current exam questions added 16 hours ago. Deciding to include EC0-349 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our EC0-349 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these EC0-349 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any ECCouncil Computer Hacking Forensic Investigator practice test comfortably within the allotted time.
Why should you never power on a computer that you need to acquire digital evidence from?
Jacob is a computer forensics investigator with over 10 years experience in investigations and has written over 50 articles on computer forensics. He has been called upon as a qualified witness to testify the accuracy and integrity of the technical log files gathered in an investigation into computer fraud. What is the term used for Jacob testimony in this case?computer fraud. What is the term used for Jacob? testimony in this case?
When investigating a network that uses DHCP to assign IP addresses, where would you look to determine which system (MAC address) had a specific IP address at a specific time?
What advantage does the tool Evidor have over the built-in Windows search?
What happens when a file is deleted by a Microsoft operating system using the FAT file system?
What hashing method is used to password protect Blackberry devices?
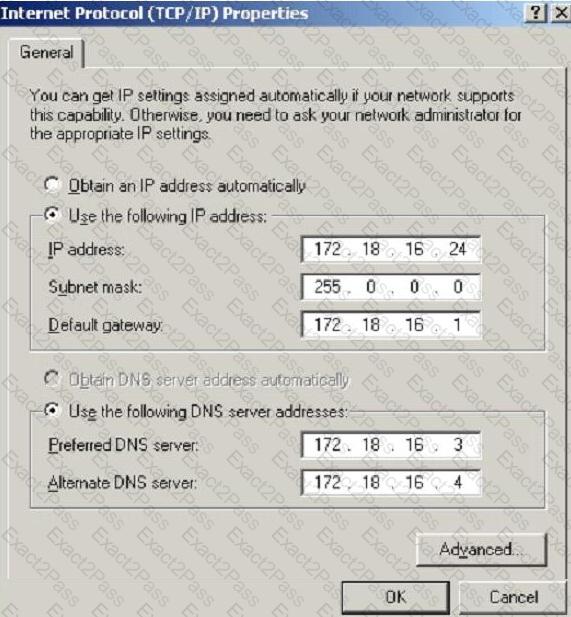
What is the CIDR from the following screenshot?