Last Update 21 hours ago Total Questions : 60
The HCIP-Security V4.0 Exam content is now fully updated, with all current exam questions added 21 hours ago. Deciding to include H12-725_V4.0 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our H12-725_V4.0 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these H12-725_V4.0 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any HCIP-Security V4.0 Exam practice test comfortably within the allotted time.
Which of the following is the function of Message 1 and Message 2 during IKEv1 phase-1 negotiation in main mode?
When Eth-Trunk is deployed for the heartbeat links between firewalls, the Eth-Trunk interface can be configured as a Layer 2 interface as long as the total bandwidth of active links on the Eth-Trunk is greater than 30% of the bandwidth required by service traffic.
Which of the following is not a process for remote users to access intranet resources through SSL VPN?
HWTACACS is a centralized information exchange protocol based on the client/server structure. It uses UDP for transmission and performs authentication, authorization, and accounting for users accessing the Internet through Point-to-Point Protocol (PPP) or Virtual Private Dial-up Network (VPDN) and administrative users logging in to devices.
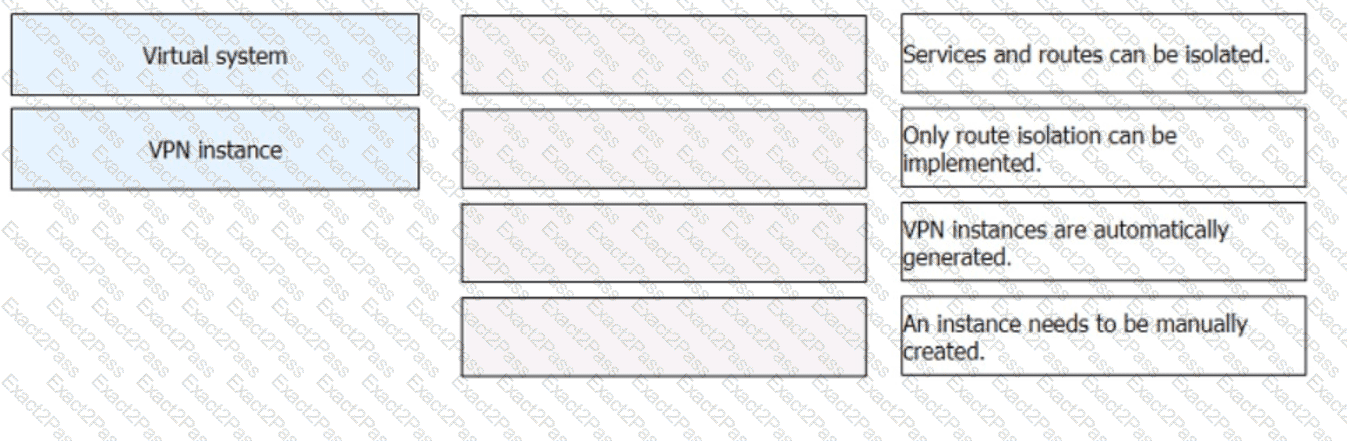
: 51 DRAG DROP
Match the description about virtual systems and VPN instances.
Which of the following parameters is not required for an IKE proposal?
The Nginx application is deployed on a Linux host. By checking Nginx logs, O & M engineers can obtain the complete URL information submitted by users and determine whether the Linux host is under SQL injection attacks.
Which of the following statements is false about virtual system resource allocation?

