Last Update 20 hours ago Total Questions : 60
The HCIP-Security V4.0 Exam content is now fully updated, with all current exam questions added 20 hours ago. Deciding to include H12-725_V4.0 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our H12-725_V4.0 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these H12-725_V4.0 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any HCIP-Security V4.0 Exam practice test comfortably within the allotted time.
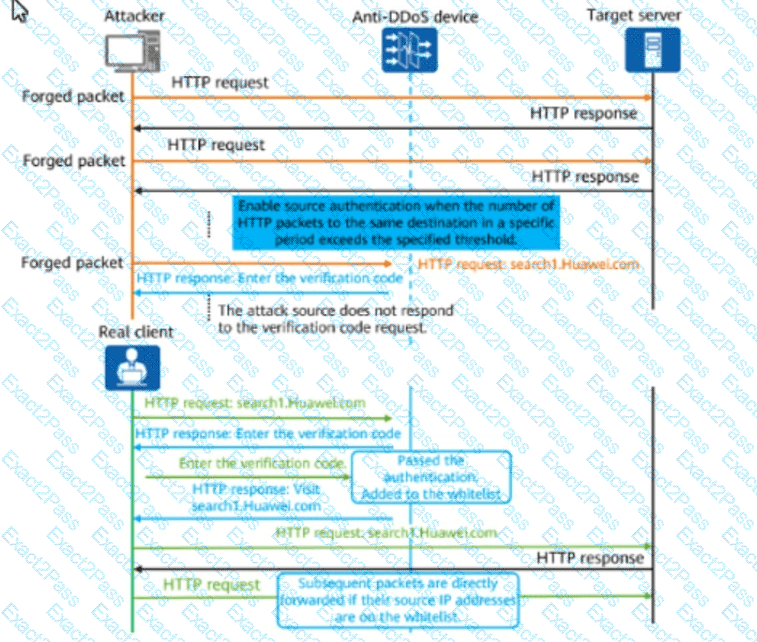
The figure shows the defense mechanism of an HTTP flood attack. Which source IP detection technology is displayed in the figure?
Which of the following statements is false about web rewriting in web proxy?
* In the data filtering profile on the firewall, keyword group "Keyword" is invoked in the upload direction of HTTP applications, the action is block, and the keyword group is invoked in the security policy. Given this, if the regular expression "b.d" is configured in the keyword group "Keyword,” which of the following texts can be posted by internal employees on the forum?
During deployment of Portal authentication, an authentication-free rule profile needs to be configured to ensure Portal pages can be opened on authentication terminals. To achieve this purpose, the following traffic needs to be permitted in the authentication-free rule profile: DNS resolution traffic of user terminals, traffic from user terminals for accessing Portal pages, and traffic from user terminals to the RADIUS server.
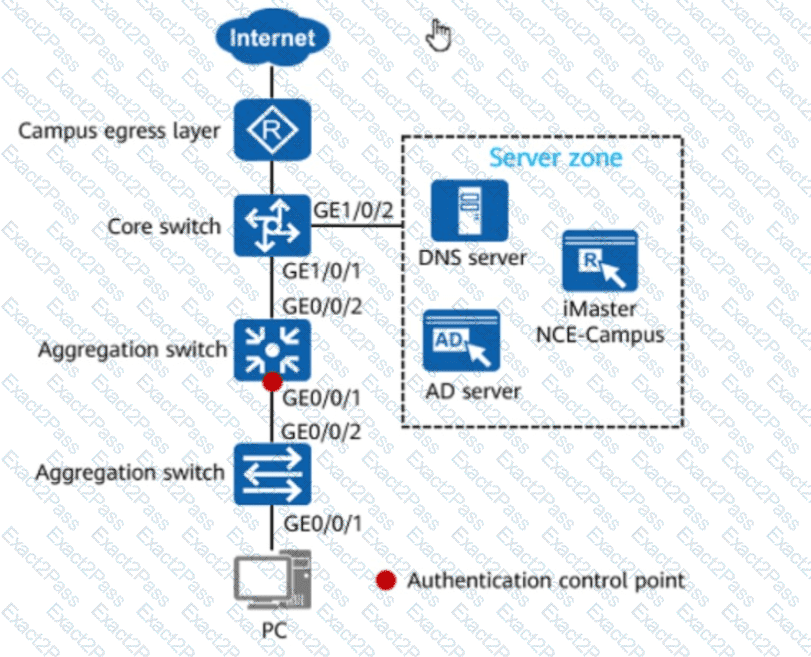
In the figure, if 802.1X authentication is used for wired users on the network, the network admission device and terminals must be connected through a Layer 2 network.
Options:
On a WLAN where the WAC has Portal authentication configured, VLAN authorization can be implemented with no additional configuration required. After Portal authentication is complete, the WAC forwards STA traffic based on the authorized VLANs.
Multiple links can be deployed at the egress of an enterprise network to improve network reliability.

