Last Update 19 hours ago Total Questions : 285
The HashiCorp Certified: Vault Associate (003)Exam content is now fully updated, with all current exam questions added 19 hours ago. Deciding to include HCVA0-003 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our HCVA0-003 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these HCVA0-003 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any HashiCorp Certified: Vault Associate (003)Exam practice test comfortably within the allotted time.
A Jenkins server is using the following token to access Vault. Based on the lookup shown below, what type of token is this? $ vault token lookup hvs.FGP1A77Hxa1Sp6Pkp1yURcZB
Key Value
--- -----
accessor RnH8jtgrxBrYanizlyJ7Y8R
creation_time 1604604512
creation_ttl 24h
display_name token
entity_id n/a
expire_time 2025-11-06T14:28:32.8891566-05:00
explicit_max_ttl 0s
id hvs.FGP1A77Hxa1Sp6KRau5eNB
issue_time 2025-11-06T14:28:32.8891566-05:00
meta < nil >
num_uses 0
orphan false
path auth/token/create
period 24h
policies [admin default]
renewable true
ttl 23h59m50s
type service
By default, what TCP port does Vault replication use?
You want to integrate a third-party application to retrieve credentials from the HashiCorp Vault API. How can you accomplish this without having direct access to the source code?
From the options below, select the benefits of using the PKI (x.509 certificates) secrets engine (select three):
You are deploying Vault in a local data center, but want to be sure you have a secondary Vault cluster in the event the primary cluster goes offline. In the secondary data center, you have applications that are running, as they are architected to run active/active. Which type of replication would be best in this scenario?
True or False? The Vault Secrets Operator does NOT encrypt client cache, such as Vault tokens and leases, by default in Kubernetes Secrets.
True or False? Once you create a KV v1 secrets engine and place data in it, there is no way to modify the mount to include the features of a KV v2 secrets engine.
Which of the following Vault policies will allow a Vault client to read a secret stored at secrets/applications/app01/api_key?
What is the proper command to enable the AWS secrets engine at the default path?
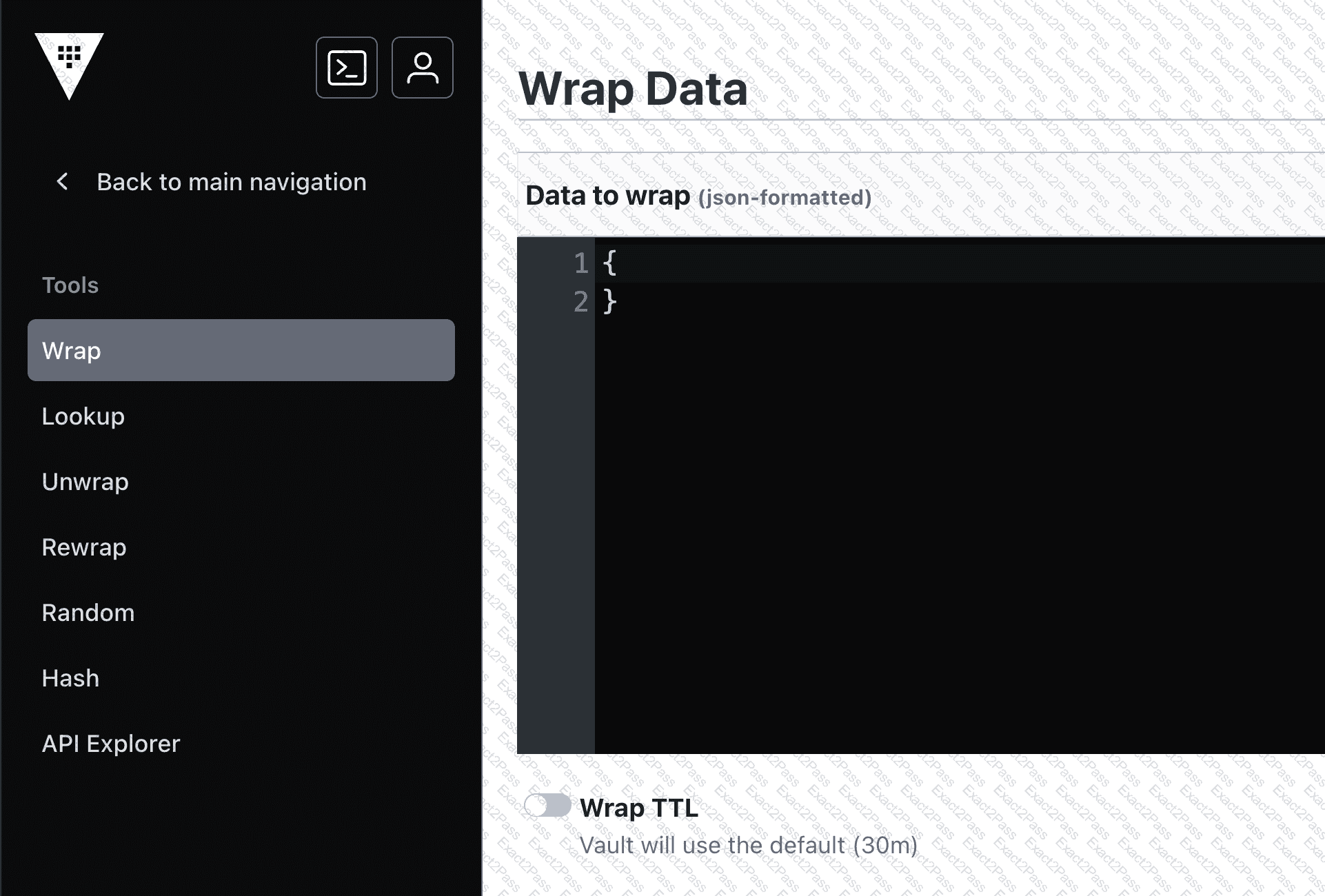
What could you do with the feature found in the screenshot below (select two)?