Last Update 1 day ago Total Questions : 531
The Computer Hacking Forensic Investigator content is now fully updated, with all current exam questions added 1 day ago. Deciding to include 312-49 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 312-49 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 312-49 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Computer Hacking Forensic Investigator practice test comfortably within the allotted time.
When a user deletes a file, the system creates a $I file to store its details. What detail does the $I file not contain?
Bob has been trying to penetrate a remote production system for the past two weeks. This time however, he is able to get into the system. He was able to use the System for a period of three weeks. However, law enforcement agencies were recoding his every activity and this was later presented as evidence.
The organization had used a Virtual Environment to trap Bob. What is a Virtual Environment?
An expert witness is a __________________ who is normally appointed by a party to assist the formulation and preparation of a party’s claim or defense.
A forensic examiner is examining a Windows system seized from a crime scene. During the examination of a suspect file, he discovered that the file is password protected. He tried guessing the password using the suspect’s available information but without any success. Which of the following tool can help the investigator to solve this issue?
If you see the files Zer0.tar.gz and copy.tar.gz on a Linux system while doing an investigation, what can you conclude?
What are the security risks of running a " repair " installation for Windows XP?
Raw data acquisition format creates _________ of a data set or suspect drive.
Which of the following tool creates a bit-by-bit image of an evidence media?
Which tool does the investigator use to extract artifacts left by Google Drive on the system?
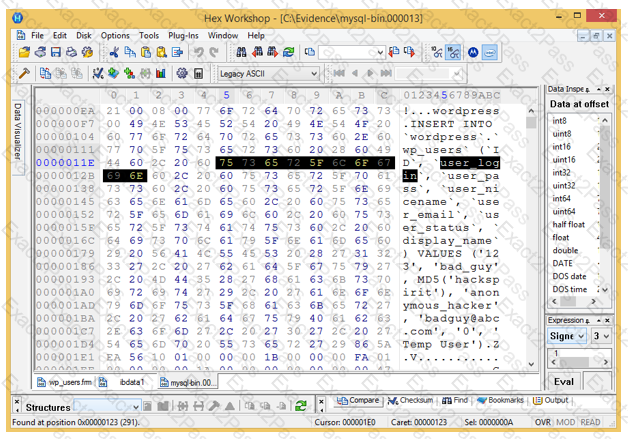
Analyze the hex representation of mysql-bin.000013 file in the screenshot below. Which of the following will be an inference from this analysis?
Which of the following is a precomputed table containing word lists like dictionary files and brute force lists and their hash values?
What type of equipment would a forensics investigator store in a StrongHold bag?
The offset in a hexadecimal code is:
Which of the following is a list of recently used programs or opened files?
You are a security analyst performing a penetration tests for a company in the Midwest. After some initial reconnaissance, you discover the IP addresses of some Cisco routers used by the company. You type in the following URL that includes the IP address of one of the routers:
http://172.168.4.131/level/99/exec/show/config
After typing in this URL, you are presented with the entire configuration file for that router. What have you discovered?

