Last Update 1 day ago Total Questions : 531
The Computer Hacking Forensic Investigator content is now fully updated, with all current exam questions added 1 day ago. Deciding to include 312-49 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 312-49 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 312-49 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Computer Hacking Forensic Investigator practice test comfortably within the allotted time.
Which of the following setups should a tester choose to analyze malware behavior?
Casey has acquired data from a hard disk in an open source acquisition format that allows her to generate compressed or uncompressed image files. What format did she use?
Who is responsible for the following tasks?
Secure the scene and ensure that is maintained in a secure state until the Forensic Team advises
Make notes about the scene that will eventually be handed over to the Forensic Team
On an Active Directory network using NTLM authentication, where on the domain controllers are the passwords stored?
What is the size value of a nibble?
What term is used to describe a cryptographic technique for embedding information into something else for the sole purpose of hiding that information from the casual observer?
The following is a log file screenshot from a default installation of IIS 6.0.
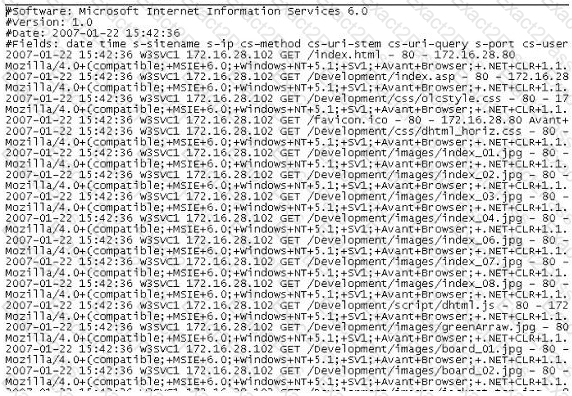
What time standard is used by IIS as seen in the screenshot?
A law enforcement officer may only search for and seize criminal evidence with _______________________, which are facts or circumstances that would lead a reasonable person to believe a crime has been committed or is about to be committed, evidence of the specific crime exists and the evidence of the specific crime exists at the place to be searched.
Which of the following does not describe the type of data density on a hard disk?
Which of the following examinations refers to the process of providing the opposing side in a trial the opportunity to question a witness?
Hackers can gain access to Windows Registry and manipulate user passwords, DNS settings, access rights or others features that they may need in order to accomplish their objectives. One simple method for loading an application at startup is to add an entry (Key) to the following Registry Hive:
Preparing an image drive to copy files to is the first step in Linux forensics. For this purpose, what would the following command accomplish?
dcfldd if=/dev/zero of=/dev/hda bs=4096 conv=noerror, sync
Which of the following techniques delete the files permanently?
Graphics Interchange Format (GIF) is a ____ RGB bitmap image format for images with up to 256 distinct colors per frame.
Why would you need to find out the gateway of a device when investigating a wireless attack?

