Last Update 2 hours ago Total Questions : 528
The Certified Ethical Hacker Exam (CEH v11) content is now fully updated, with all current exam questions added 2 hours ago. Deciding to include 312-50v11 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 312-50v11 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 312-50v11 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Certified Ethical Hacker Exam (CEH v11) practice test comfortably within the allotted time.
env x=’(){ :;};echo exploit’ bash –c ‘cat/etc/passwd’
What is the Shellshock bash vulnerability attempting to do on a vulnerable Linux host?
if you send a TCP ACK segment to a known closed port on a firewall but it does not respond with an RST. what do you know about the firewall you are scanning?
When configuring wireless on his home router, Javik disables SSID broadcast. He leaves authentication “open” but sets the SSID to a 32-character string of random letters and numbers.
What is an accurate assessment of this scenario from a security perspective?
What does a firewall check to prevent particular ports and applications from getting packets into an organization?
Which mode of IPSec should you use to assure security and confidentiality of data within the same LAN?
ViruXine.W32 virus hides their presence by changing the underlying executable code.
This Virus code mutates while keeping the original algorithm intact, the code changes itself each time it runs, but the function of the code (its semantics) will not change at all.
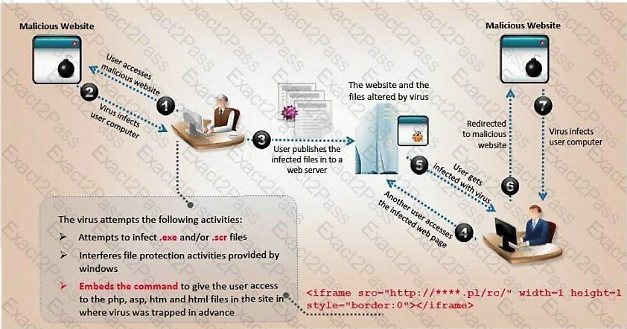
Here is a section of the Virus code:
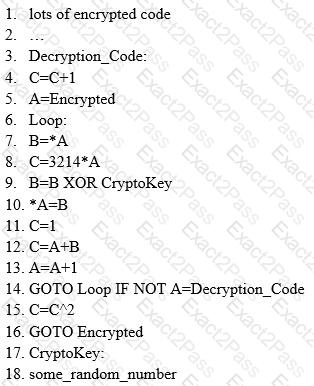
What is this technique called?
If a token and 4-digit personal identification number (PIN) are used to access a computer system and the token performs off-line checking for the correct PIN, what type of attack is possible?
Annie, a cloud security engineer, uses the Docker architecture to employ a client/server model in the application she is working on. She utilizes a component that can process API requests and handle various Docker objects, such as containers, volumes. Images, and networks. What is the component of the Docker architecture used by Annie in the above scenario?

