Last Update 20 hours ago Total Questions : 217
The Huawei Certified ICT Professional - Constructing Infrastructure of Security Network content is now fully updated, with all current exam questions added 20 hours ago. Deciding to include H12-721 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our H12-721 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these H12-721 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Huawei Certified ICT Professional - Constructing Infrastructure of Security Network practice test comfortably within the allotted time.
What are the three elements of an abnormal flow cleaning solution?
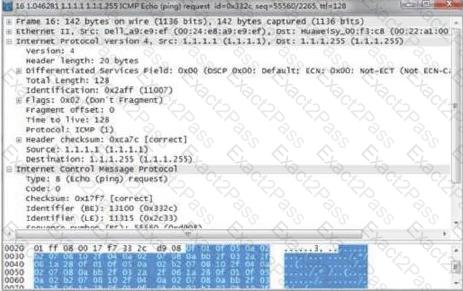
When an attack occurs, the result of packet capture on the attacked host (1.1.1.1) is as shown in the figure. What kind of attack is this attack?
Connecting the internal network interface address from the firewall By pinging the internal network address of the peer, the IPSec tunnel can be successfully triggered. The internal PC cannot trigger the tunnel establishment. What are the possible reasons?
Which of the following is correct about the configuration of the firewall interface bound to the VPN instance?
When the firewall works in the dual-system hot backup load balancing environment, if the upstream and downstream routers are working in the routing mode, you need to adjust the OSPF cost based on HRP.
The ip-link sends a probe packet to the specified IP address. By default, after 3 probe failures, the link to this IP address is considered faulty.
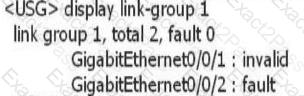
After the link-group is configured on the device, use the display link-group 1 command to obtain the following information. What information can I get?
What is the correct statement about the binding of local users to VPN instances?
Site to Site IPSec VPN Tunnel Negotiation Fails. How do I view the establishment and configuration of the IKE Phase 2 security association?
Which of the following does the virtual firewall technical feature not include?

