Last Update 20 hours ago Total Questions : 217
The Huawei Certified ICT Professional - Constructing Infrastructure of Security Network content is now fully updated, with all current exam questions added 20 hours ago. Deciding to include H12-721 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our H12-721 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these H12-721 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Huawei Certified ICT Professional - Constructing Infrastructure of Security Network practice test comfortably within the allotted time.
The administrator can create vfw1 and vfw2 on the root firewall to provide secure multi-instance services for enterprise A and enterprise B, and configure secure forwarding policies between security zones of vfw1 and vfw2.
Defense against the cache server The main method of DNS request flood is to use the DNS source authentication technology:
Which of the following IKE Negotiation Phase 1 main mode negotiation processes is the role of Message 5 and Message 6?
The virtual firewall forwards multiple instances. The firewall has multiple routing tables and forwarding tables. The addresses are overlapped and are implemented on the same configuration interface. Users with configuration rights can configure and view all data.
Which of the following states indicates that a BFD session has been successfully established?
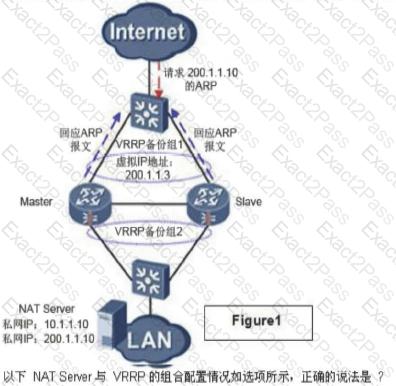
In a dual-system hot standby network, the NAT configurations of the two USGs are consistent. When the address in the NAT address pool is on the same network segment as the virtual IP address of the VRRP backup group, the next two graphs show the ARP response of the NAT server and VRRP combination application (lack of a picture).
Which is incorrect about the IKE DPD statement?
112. The ESP only verifies the IP payload and can perform NAT traversal, but the ESP encrypts the Layer 4 port information and causes the PAT function to be unusable. This problem can be solved by using the IPSec transparent NAT function, which encapsulates the ESP packet in the UDP header and comes with the necessary port information to make the PAT work normally.
An enterprise network is as follows. Firewall A and firewall B establish an IPSec VPN. After the IPSec configuration is complete, the administrator needs to test the connectivity of the IPSec VPN. Generally, the firewall needs to simulate the traffic of the server A to access the intranet server B. The administrator can use which of the following ping commands.

In the first phase of IKE V1, the pre-shared key master mode exchange process, in which message is the SA payload sent?

