Last Update 20 hours ago Total Questions : 217
The Huawei Certified ICT Professional - Constructing Infrastructure of Security Network content is now fully updated, with all current exam questions added 20 hours ago. Deciding to include H12-721 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our H12-721 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these H12-721 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Huawei Certified ICT Professional - Constructing Infrastructure of Security Network practice test comfortably within the allotted time.
In the DDoS attack defense, if the service learning function is used to find that there is no service or traffic of a certain service in normal traffic, you can use the blocking or traffic limiting method to defend against attacks on the Anti-DDoS device. .
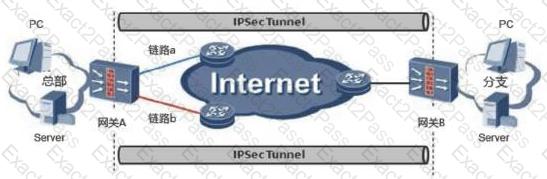
In the IPSec active/standby link backup application scenario, gateway B uses IPSec tunneling technology and gateway A to establish an IPSec VPN.
An enterprise network is as follows. At this time, server A cannot access server B. The administrator performs troubleshooting. It finds that server A can access firewall A, but cannot access firewall B. What is the method for administrators to use to troubleshoot problems?

IPSec NAT traversal does not support IKE main mode, aggressive mode IP address + pre-shared key mode authentication, because pre-shared key mode authentication needs to extract the source IP address in the IP address to find the pre-shared key corresponding to this address. . The address change caused by the presence of NAT prevents the device from finding the pre-shared key.
In Huawei ' s abnormal traffic cleaning solution, the characteristics of the straight-line deployment mode and the bypass deployment mode are correct.
The constraints of the policy in the traffic limiting policy include quintuple, time period, user identity, and application protocol.
The load balancing function is configured on the USG firewall for three FTP servers. The IP addresses and weights of the three physical servers are 10.1.13/24 (weight 16); 10.1.1.4/24 (weight 32); 10.1.1.5 /24 (weight 16), and the virtual server address is 202.152.26.123/24. A PC with the host address of 202.152.26.3/24 initiates access to the FTP server. Run the display firewall session table command on the firewall to check the configuration. Which of the following conditions indicates that the load balancing function is successfully implemented?
Which of the following is the correct description of the SMURF attack?
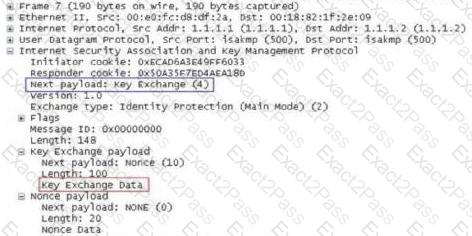
The following figure shows the data packet of the pre-shared key mode main mode exchange process in the first phase of IKE V1. What is captured below?
Huawei ' s abnormal traffic cleaning solution must deploy an independent testing center.

