Last Update 12 hours ago Total Questions : 546
The Microsoft 365 Administrator Exam content is now fully updated, with all current exam questions added 12 hours ago. Deciding to include MS-102 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our MS-102 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these MS-102 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Microsoft 365 Administrator Exam practice test comfortably within the allotted time.
Which role should you assign to User1?
Available Choices (select all choices that are correct)
You need to protect the U.S. PII data to meet the technical requirements.
What should you create?
HOTSPOT
You create the Microsoft 365 tenant.
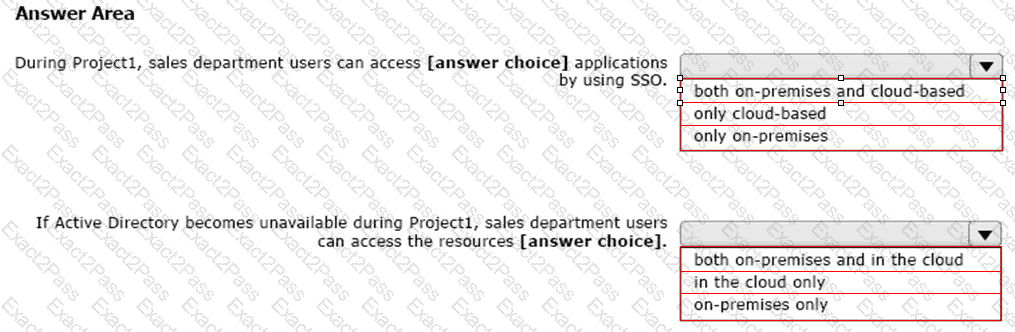
You implement Azure AD Connect as shown in the following exhibit.

Use the drop-down menus to select the answer choice that completes each statement based on the information presented in the graphic.
NOTE: Each correct selection is worth one point.
Which report should the New York office auditors view?
You need to ensure that all the sales department users can authenticate successfully during Project1 and Project2.
Which authentication strategy should you implement for the pilot projects?
You have a Microsoft 365 E5 subscription that contains 200 Android devices enrolled in Microsoft Intune.
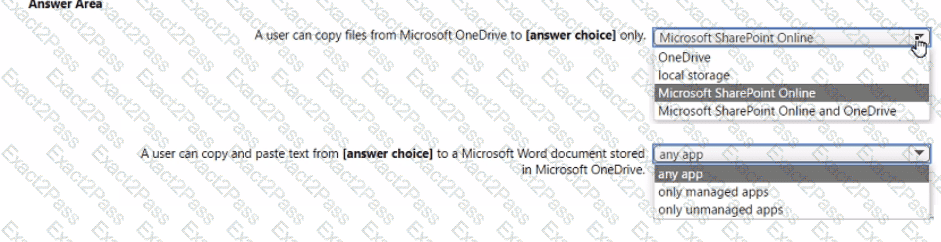
You create an Android app protection policy named Policy! that is targeted to all Microsoft apps and assigned to all users.
Policy! has the Data protection settings shown in the following exhibit.

Use the drop-down menus to select ' he answer choice that completes each statement based on the information presented in the graphic.
You have a Microsoft 365 E5 subscription that contains Windows 11 devices. All the devices are onboarded to Microsoft Defender for Endpoint.
You need to compare the configuration of the devices against industry standard benchmarks. What should you use?
You use Microsoft Defender for Endpoint.
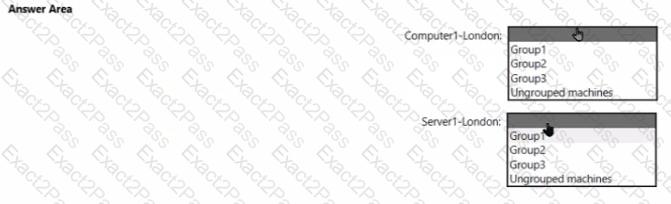
You have the Microsoft Defender for Endpoint device groups shown in the following table
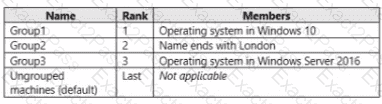
You plan to onboard computers to Microsoft Defender for Endpoint as shown in the following table.
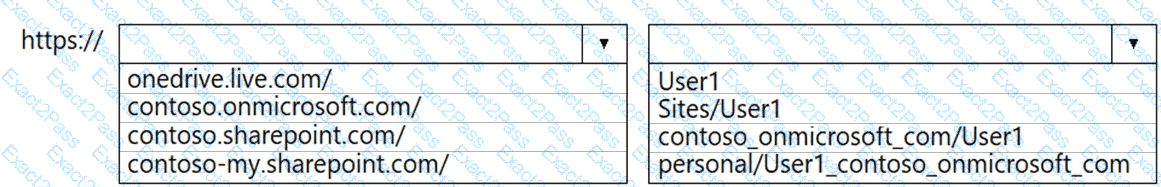
You have a Microsoft 365 subscription that links to an Azure Active Directory (Azure AD) tenant named contoso.onmicrosoft.com.
A user named User1 stores documents in Microsoft OneDrive.
You need to place the contents of User1’s OneDrive account on an eDiscovery hold.
Which URL should you use for the eDiscovery hold? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have a Microsoft 365 subscription that contains the users shown in the following table.
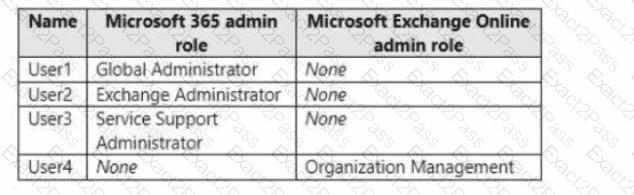
You plan to use Exchange Online to manage email for a DNS domain.
An administrator adds the DNS domain to the subscription.
The DNS domain has a status of Incomplete setup.
You need to identify which user can complete the setup of the DNS domain. The solution must use the principle of least privilege.
Which user should you identify?

