Last Update 22 hours ago Total Questions : 68
The Netskope Certified Cloud Security Architect Exam content is now fully updated, with all current exam questions added 22 hours ago. Deciding to include NSK300 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our NSK300 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these NSK300 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Netskope Certified Cloud Security Architect Exam practice test comfortably within the allotted time.
What is a Fast Scan component of Netskope Threat Detection?
You want to integrate with a third-party DLP engine that requires ICAP. In this scenario, which Netskope platform component must be configured?
A company needs to block access to their instance of Microsoft 365 from unmanaged devices. They have configured Reverse Proxy and have also created a policy that blocks login activity for the AD group " marketing-users " for the Reverse Proxy access method. During UAT testing, they notice that access from unmanaged devices to Microsoft 365 is not blocked for marketing users.
What is causing this issue?
You configured a pair of IPsec funnels from the enterprise edge firewall to a Netskope data plane. These tunnels have been implemented to steer traffic for a set of defined HTTPS SaaS applications accessed from end-user devices that do not support the Netskope Client installation. You discover that all applications steered through this tunnel are non-functional.
According to Netskope. how would you solve this problem?
Your customer is currently using Directory Importer with Active Directory (AD) to provision users to Nelskope. They have recently acquired three new companies (A. B. and C) and want to onboard users from the companies onto the NetsKope platform. Information about the companies is shown below.
- Company A uses Active Directory.
-- Company B uses Azure AD.
-- Company C uses Okta Universal Directory.
Which statement is correct in this scenario?
You are deploying the Netskope Client to Windows devices. The following command line would be used to install the client MSI file:

In this scenario, what is < token > referring to in the command line?
Review the exhibit.
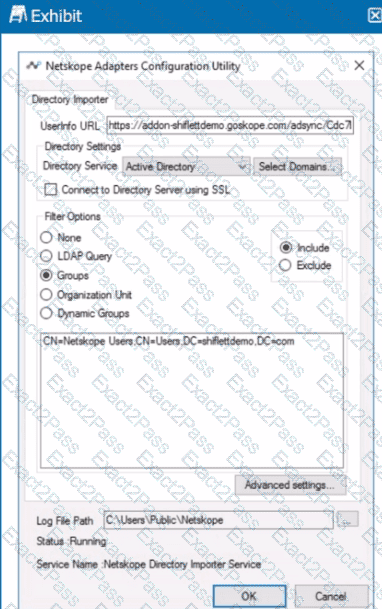
You installed Directory Importer and configured it to import specific groups ot users into your Netskope tenant as shown in the exhibit. One hour after a new user has been added to the domain, the user still has not been provisioned to Netskope.
What are three potential reasons for this failure? (Choose three.)

