Last Update 16 hours ago Total Questions : 115
The Palo Alto Networks System Engineer - Prisma CloudProfessional content is now fully updated, with all current exam questions added 16 hours ago. Deciding to include PSE-Prisma-Pro-24 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our PSE-Prisma-Pro-24 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these PSE-Prisma-Pro-24 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Palo Alto Networks System Engineer - Prisma CloudProfessional practice test comfortably within the allotted time.
Which filter type is valid in Asset Explorer?
Which statement applies to vulnerability management policies?
The following error is received when performing a manual twistcli scan on an image:
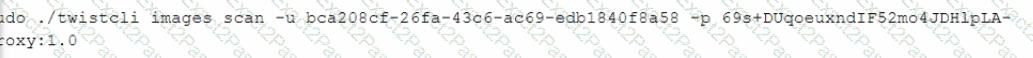
What is missing from the command?
Which Amazon Web Services (AWS) service supplies information for Prisma Cloud "event where" Resource Query Language (RQL) queries?
What are the asset severity levels within Prisma Cloud asset inventory?
Which type of Resource Query Language (RQL) query is used to create a custom policy that looks for untagged resources?
Which statement explains the correlation between the block and alert thresholds in a vulnerability management policy?

