Last Update 16 hours ago Total Questions : 119
The LPIC-2 - Exam 202 (part 2 of 2), version 4.5 content is now fully updated, with all current exam questions added 16 hours ago. Deciding to include 202-450 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 202-450 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 202-450 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any LPIC-2 - Exam 202 (part 2 of 2), version 4.5 practice test comfortably within the allotted time.
Which directive in a Nginx server configuration block defines the TCP ports on which the virtual host will be available, and which protocols it will use? (Specify ONLY the option name without any values.)
What information can be found in the file specified by the status parameter in an OpenVPN server configuration file? (Choose two.)
The Samba configuration file contains the following lines:
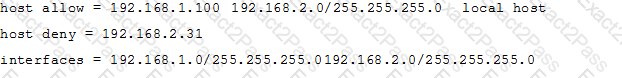
A workstation is on the wired network with an IP address of 192.168.1.177 but is unable to access the Samba server. A wireless laptop with an IP address 192.168.2.93 can access the Samba server. Additional trouble shooting shows that almost every machine on the wired network is unable to access the Samba server.
Which alternate host allow declaration will permit wired workstations to connect to the Samba server without denying access to anyone else?
Which of the following PAM modules allows the system administrator to use an arbitrary file containing a list of user and group names with restrictions on the system resources available to them?
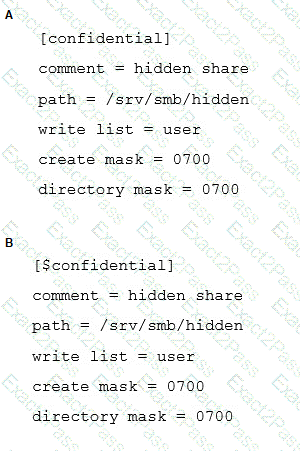
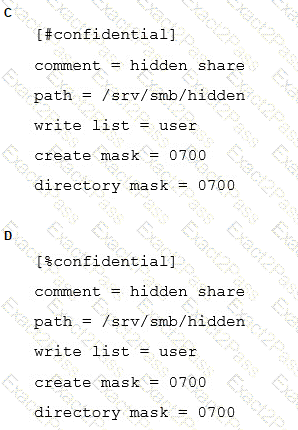
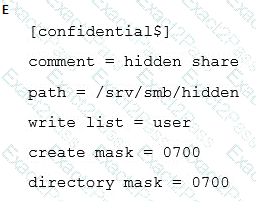
A user requests a “hidden” Samba share, named confidential, similar to the Windows Administration Share. How can this be configured?
When are Sieve filters usually applied to an email?
Which netfilter table contains built-in chains called INPUT, OUTPUT and FORWARD?
Which Linux user is used by vsftpd to perform file system operations for anonymous FTP users?
It has been discovered that the company mail server is configured as an open relay. Which of the following actions would help prevent the mail server from being used as an open relay while maintaining the possibility to receive company mails? (Choose two.)
What is the name of the network security scanner project which, at the core, is a server with a set of network vulnerability tests?

