Last Update 16 hours ago Total Questions : 119
The LPIC-2 - Exam 202 (part 2 of 2), version 4.5 content is now fully updated, with all current exam questions added 16 hours ago. Deciding to include 202-450 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 202-450 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 202-450 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any LPIC-2 - Exam 202 (part 2 of 2), version 4.5 practice test comfortably within the allotted time.
Which statements about the Alias and Redirect directives in Apache HTTPD’s configuration file are true? (Choose two.)
Which configuration parameter on a Postfix server modifies only the sender address and not the recipient address?
There is a restricted area in a site hosted by Apache HTTPD, which requires users to authenticate against the file /srv/www/security/sitepasswd.
Which command is used to CHANGE the password of existing users, without losing data, when Basic authentication is being used?
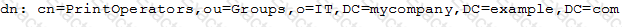
Which of the following is correct about this excerpt from an LDIF file?
Which OpenLDAP client command can be used to change the password for an LDAP entry? (Specify ONLY the command without any path or parameters.)
When the default policy for the netfilter INPUT chain is set to DROP, why should a rule allowing traffic to localhost exist?
The following Apache HTTPD configuration has been set up to create a virtual host available at www.example.com and www2.example.com:
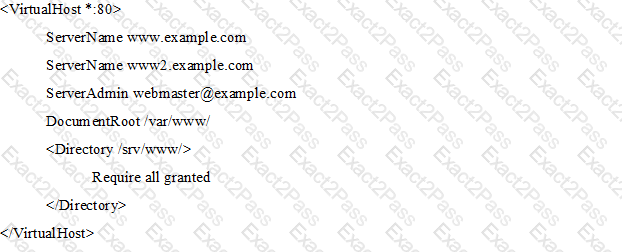
Even though Apache HTTPD correctly processed the configuration file, requests to both names are not handled correctly. What should be changed in order to ensure correct operations?
Which of the following actions are available in Sieve core filters? (Choose three.)
What is DNSSEC used for?
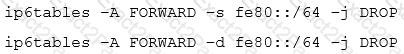
Which of the statements below are correct regarding the following commands, which are executed on a Linux router? (Choose two.)