Last Update 20 hours ago Total Questions : 704
The Computer Hacking Forensic Investigator (CHFI-v10) content is now fully updated, with all current exam questions added 20 hours ago. Deciding to include 312-49v10 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 312-49v10 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 312-49v10 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Computer Hacking Forensic Investigator (CHFI-v10) practice test comfortably within the allotted time.
During an investigation of an XSS attack, the investigator comes across the term “[a-zA-Z0-9\%]+” in analyzed evidence details. What is the expression used for?
Which of the following file formats allows the user to compress the acquired data as well as keep it randomly accessible?
Brian needs to acquire data from RAID storage. Which of the following acquisition methods is recommended to retrieve only the data relevant to the investigation?
Smith is an IT technician that has been appointed to his company ' s network vulnerability assessment team. He is the only IT employee on the team. The other team members include employees from
Accounting, Management, Shipping, and Marketing. Smith and the team members are having their first meeting to discuss how they will proceed. What is the first step they should do to create the network
vulnerability assessment plan?
As a Certified Ethical Hacker, you were contracted by a private firm to conduct an external security assessment through penetration testing . What document describes the specifics of the testing, the associated violations, and essentially protects both the organization’s interest and your liabilities as a tester?
What does the command “C:\ > wevtutil gl < log name > ” display?
What is the investigator trying to view by issuing the command displayed in the following screenshot?

Jim’s company regularly performs backups of their critical servers. But the company can’t afford to send backup tapes to an off-site vendor for long term storage and archiving. Instead Jim’s company keeps the backup tapes in a safe in the office. Jim’s company is audited each year, and the results from this year’s audit show a risk because backup tapes aren’t stored off-site. The Manager of Information Technology has a plan to take the backup tapes home with him and wants to know what two things he can do to secure the backup tapes while in transit?
Harold is finishing up a report on a case of network intrusion, corporate spying, and embezzlement that he has been working on for over six months. He is trying to find the right term to use in his report to describe network-enabled spying. What term should Harold use?
Which of the following commands shows you all of the network services running on Windows-based servers?
Which code does the FAT file system use to mark the file as deleted?
An expert witness is a __________________ who is normally appointed by a party to assist the formulation and preparation of a party’s claim or defense.
All Blackberry email is eventually sent and received through what proprietary RIM-operated mechanism?
Amber, a black hat hacker, has embedded a malware into a small enticing advertisement and posted it on a popular ad-network that displays across various websites. What is she doing?
Data is striped at a byte level across multiple drives, and parity information is distributed among all member drives.
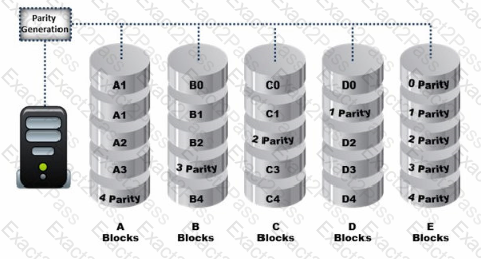
What RAID level is represented here?

