Last Update 20 hours ago Total Questions : 704
The Computer Hacking Forensic Investigator (CHFI-v10) content is now fully updated, with all current exam questions added 20 hours ago. Deciding to include 312-49v10 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 312-49v10 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 312-49v10 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Computer Hacking Forensic Investigator (CHFI-v10) practice test comfortably within the allotted time.
What is an investigator looking for in the rp.log file stored in a system running on Windows 10 operating system?
Which Event Correlation approach assumes and predicts what an attacker can do next after the attack by studying statistics and probability?
Which of the following is a responsibility of the first responder?
What value of the " Boot Record Signature " is used to indicate that the boot-loader exists?
Which of the following is a non-zero data that an application allocates on a hard disk cluster in systems running on Windows OS?
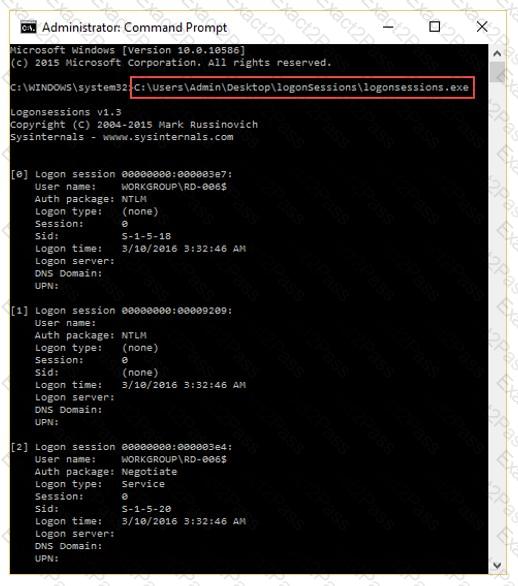
What is the investigator trying to analyze if the system gives the following image as output?
Raw data acquisition format creates _________ of a data set or suspect drive.
To reach a bank web site, the traffic from workstations must pass through a firewall. You have been asked to review the firewall configuration to ensure that workstations in network 10.10.10.0/24 can only reach the bank web site 10.20.20.1 using https. Which of the following firewall rules meets this requirement?
The efforts to obtain information before a trail by demanding documents, depositions, questioned and answers written under oath, written requests for admissions of fact and examination of the scene is a description of what legal term?
While working for a prosecutor, what do you think you should do if the evidence you found appears to be exculpatory and is not being released to the defense?
If you discover a criminal act while investigating a corporate policy abuse, it becomes a publicsector investigation and should be referred to law enforcement?
When obtaining a warrant, it is important to:
Which of the following statements is true with respect to SSDs (solid-state drives)?
Which of the following tools will allow a forensic Investigator to acquire the memory dump of a suspect machine so that It may be Investigated on a forensic workstation to collect evidentiary data like processes and Tor browser artifacts?
Which of the following is a requirement for senders as per the CAN-SPAM act?

