Last Update 23 hours ago Total Questions : 64
The CyberArk Defender Access (ACC-DEF) content is now fully updated, with all current exam questions added 23 hours ago. Deciding to include ACCESS-DEF practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our ACCESS-DEF exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these ACCESS-DEF sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any CyberArk Defender Access (ACC-DEF) practice test comfortably within the allotted time.
CyberArk Identity has created a CLI integration with which vendor?
Which device enrollment settings are valid? (Choose two.)
When a user enrolls a mobile device (iOS or Android) without enabling mobile device management, what happens? (Choose three.)
What can cause users to be prompted for unrecognized MFA factors, such as a wrong phone number or unregistered MFA factor?
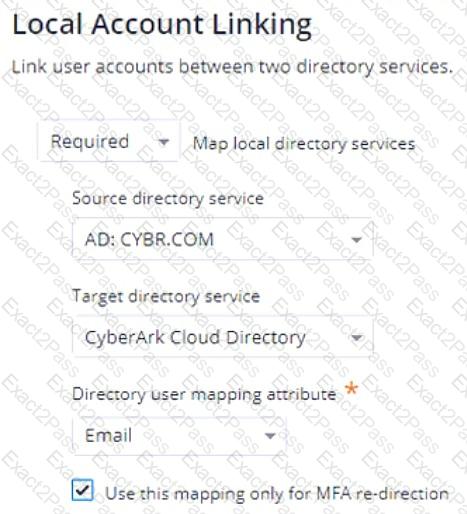
Refer to the exhibit.
If an Authentication Policy is configured as shown in the exhibit, which statement is correct?
Where can MFA filters be used? (Choose three.)
Which statement is true about the app gateway?
What does the CyberArk Identity App Gateway work with? (Choose three.)
What is the most likely reason a CyberArk Identity admin would turn on the "Provisioning" feature within a Web App connector?

