Last Update 23 hours ago Total Questions : 60
The CyberArk Sentry Secrets Manager content is now fully updated, with all current exam questions added 23 hours ago. Deciding to include SECRET-SEN practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our SECRET-SEN exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these SECRET-SEN sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any CyberArk Sentry Secrets Manager practice test comfortably within the allotted time.
When working with Summon, what is the purpose of the secrets.yml file?
An application is having authentication issues when trying to securely retrieve credential’s from the Vault using the CCP webservices RESTAPI. CyberArk Support advised that further debugging should be enabled on the CCP server to output a trace file to review detailed logs to help isolate the problem.
What best describes how to enable debug for CCP?
You have a PowerShell script that is being used on 1000 workstations. It requires a Windows Domain credential that is currently hard coded in the script.
What is the simplest solution to remove that credential from the Script?
When installing the Vault Conjur Synchronizer, you see this error:
Forbidden
Logon Token is Empty – Cannot logon
Unauthorized
What must you ensure to remediate the issue?
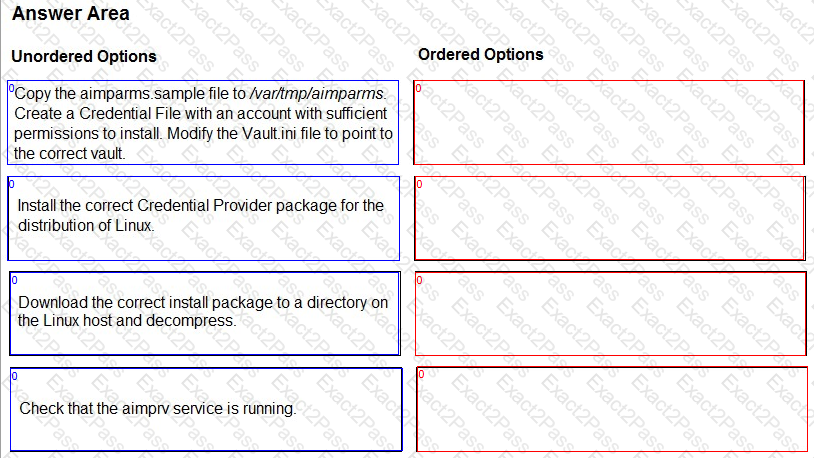
You are installing a Credential Provider on a Linux host. Arrange the installation steps in the correct sequence.
When an application is retrieving a credential from Conjur, the application authenticates to Follower A. Follower B receives the next request to retrieve the credential.
What happens next?
What does “Line of business (LOB)” represent?

