Last Update 23 hours ago Total Questions : 64
The CyberArk Defender Access (ACC-DEF) content is now fully updated, with all current exam questions added 23 hours ago. Deciding to include ACCESS-DEF practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our ACCESS-DEF exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these ACCESS-DEF sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any CyberArk Defender Access (ACC-DEF) practice test comfortably within the allotted time.
Which feature does the CyberArk Identity Connector provide?
Your organization wants to implement passwordless authentication for business critical web applications. CyberArk Identity manages access to these applications.
What can you do to facilitate the enforcement of this passwordless authentication initiative? (Choose two.)
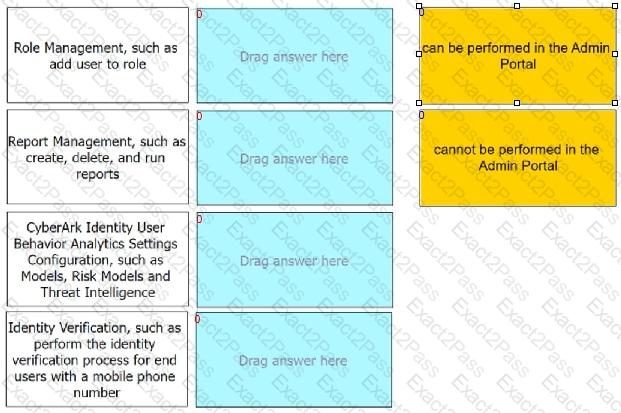
Match each listed task to indicate if an administrator can perform it in the Admin Portal.
When logging on to the User Portal, which authentication methods can enable the user to bypass authentication rules and default profile? (Choose two.)
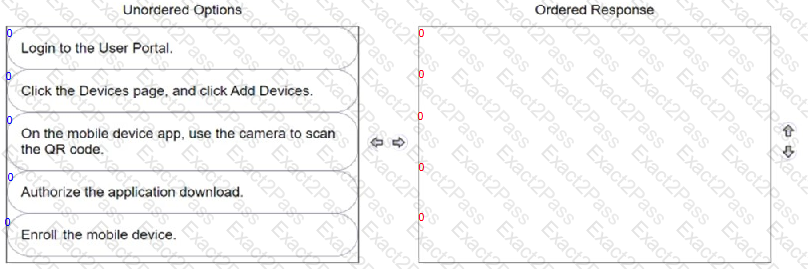
A user wants to install the CyberArk Identity mobile app by using a QR code.
Arrange the steps to do this in the correct sequence.
Your organization wants to limit access to the CyberArk Identity user portal to only corporate issued domain-joined laptops without the use of a VPN.
How can you achieve this?
Your team is deploying endpoint authentication onto the corporate endpoints within an organization. Enrollment details include when the enrollment must be completed, and the enrollment code was sent out to the users. Enrollment can be performed in the office or remotely (without the assistance of an IT support engineer). You received feedback that many users are unable to enroll into the system using the enrollment code.
What can you do to resolve this? (Choose two.)

