Last Update 3 hours ago Total Questions : 515
The Microsoft Azure Security Technologies content is now fully updated, with all current exam questions added 3 hours ago. Deciding to include AZ-500 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our AZ-500 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these AZ-500 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Microsoft Azure Security Technologies practice test comfortably within the allotted time.
You have an Azure subscription.
You create a new virtual network named VNet1.
You plan to deploy an Azure web app named App1 that will use VNet1 and will be reachable by using private IP addresses. The solution must support inbound and outbound network traffic.
What should you do?
You need to configure WebApp1 to meet the data and application requirements.
Which two actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
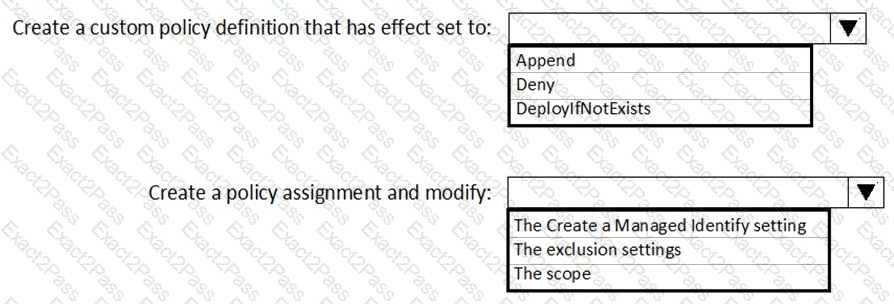
You need to deploy Microsoft Antimalware to meet the platform protection requirements.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to meet the technical requirements for VNetwork1.
What should you do first?
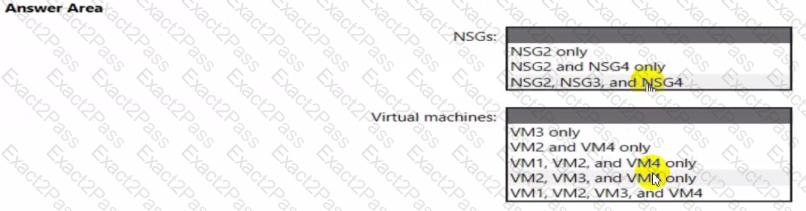
You implement the planned changes for ASG1 and ASG2.
In which NSGs can you use ASG1. and the network interfaces of which virtual machines can you assign to ASG2?
You need to implement the planned change for SQLdb1.
Which two actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
You need to implement the planned change for WAF1.
The solution must minimize administrative effort
What should you do?
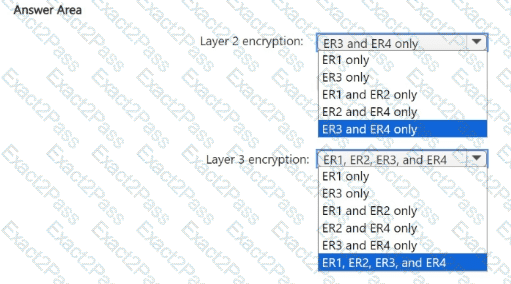
You need to recommend an encryption solution for the planned ExpressRoute implementation. The solution must meet the technical requirements.
Which ExpressRoute circuit should you recommend for each type of encryption? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You implement the planned changes for the key vaults.
To which key vaults can you restore AKV1 backups?
You need to implement the planned change for VM1 to access storage1.
The solution must meet the technical requirements.
What should you do first?

