Last Update 18 hours ago Total Questions : 203
The Administering Information Security in Microsoft 365 content is now fully updated, with all current exam questions added 18 hours ago. Deciding to include SC-401 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our SC-401 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these SC-401 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Administering Information Security in Microsoft 365 practice test comfortably within the allotted time.
You have a Microsoft 365 E5 subscription that contains a trainable classifier named Trainable1.
You plan to create the items shown in the following table.
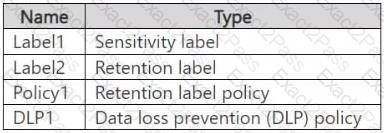
Which items can use Trainable 1?
You have a Microsoft 365 tenant.
You have a database that stores customer details. Each customer has a unique 13-digit identifier that consists of a fixed pattern of numbers and letters.
You need to implement a data loss prevention (DLP) solution that meets the following requirements:
● Email messages that contain a single customer identifier can be sent outside your company.
● Email messages that contain two or more customer identifiers must be approved by the company ' s data privacy team.
Which two components should you include in the solution? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
You have a Microsoft 365 E5 subscription.
You plan to implement Microsoft Purview Insider Risk Management.
You obtain a file named File1.csv that contains employee resignation data.
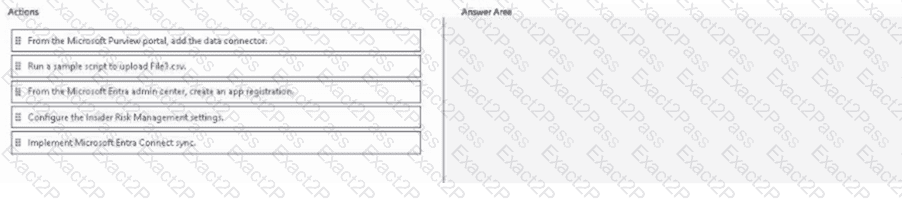
You need to implement the HR data connector and upload File1.csv by using the connector.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
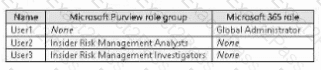
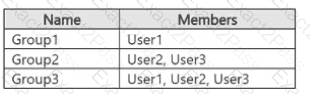
You have a Microsoft 365 E5 subscription that contains the users shown in the following table.
The subscription contains the groups shown in the following table.
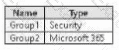
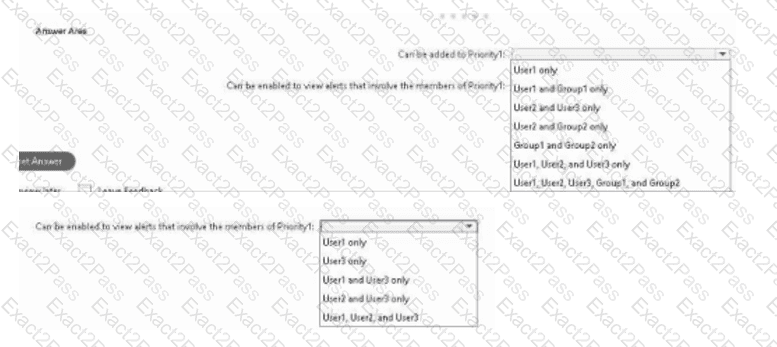
You plan to create a priority user group named Priority1.
You need to identify the following:
. Which users and groups can be added to Priority1?
. Which users can be enabled to view alerts that involve the members of Priority1?
What should you identify? To answer, select the appropriate options in the answer area.
You have a data loss prevention (DIP) policy that applies to the Devices location. The policy protects documents that contain United States passport numbers
Users report that they cannot upload documents to a travel management website because of the pokey.
You need to ensure that the users can upload the documents to the travel management website. The solution must prevent the protected content from being uploaded to other locations.
Which Microsoft 365 Endpoint data loss prevention (Endpoint DIP) setting should you configure?
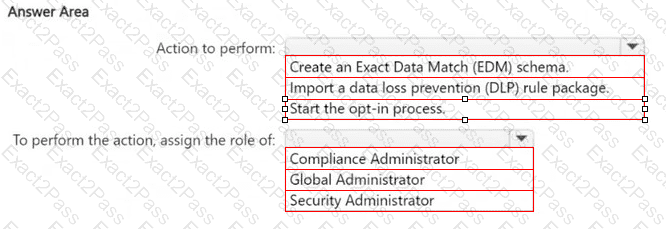
You have a new Microsoft 365 E5 tenant.
You need to create a custom trainable classifier that will detect product order forms. The solution must use the principle of least privilege.
What should you do first? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to be alerted when users share sensitive documents from Microsoft OneDrive to any users outside your company.
What should you do?

