Last Update 17 hours ago Total Questions : 878
The Certified Ethical Hacker (CEH) content is now fully updated, with all current exam questions added 17 hours ago. Deciding to include CEH-001 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our CEH-001 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these CEH-001 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Certified Ethical Hacker (CEH) practice test comfortably within the allotted time.
Which of the following Netcat commands would be used to perform a UDP scan of the lower 1024 ports?
Which of the following are well know password-cracking programs?(Choose all that apply.
As a securing consultant, what are some of the things you would recommend to a company to ensure DNS security? Select the best answers.
You are a Administrator of Windows server. You want to find the port number for POP3. What file would you find the information in and where?
Select the best answer.
You want to use netcat to generate huge amount of useless network data continuously for various performance testing between 2 hosts.
Which of the following commands accomplish this?
Sniffing is considered an active attack.
Which of the following keyloggers cannot be detected by anti-virus or anti-spyware products?
What is the algorithm used by LM for Windows2000 SAM?
Exhibit:
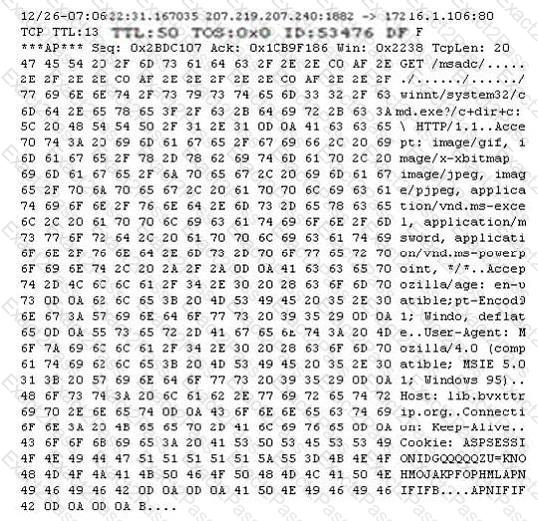
Study the following log extract and identify the attack.
When Jason moves a file via NFS over the company ' s network, you want to grab a copy of it by sniffing. Which of the following tool accomplishes this?
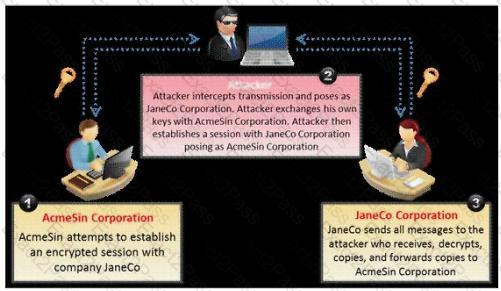
What type of attack is shown in the following diagram?
In what stage of Virus life does a stealth virus gets activated with the user performing certain actions such as running an infected program?
Which of the following statements would NOT be a proper definition for a Trojan Horse?
SNMP is a connectionless protocol that uses UDP instead of TCP packets (True or False)
Neil is a network administrator working in Istanbul. Neil wants to setup a protocol analyzer on his network that will receive a copy of every packet that passes through the main office switch. What type of port will Neil need to setup in order to accomplish this?
Which of the following type of scanning utilizes automated process of proactively identifying vulnerabilities of the computing systems present on a network?
What does ICMP (type 11, code 0) denote?
Jack Hacker wants to break into Brown Co. ' s computers and obtain their secret double fudge cookie recipe. Jack calls Jane, an accountant at Brown Co., pretending to be an administrator from Brown Co. Jack tells Jane that there has been a problem with some accounts and asks her to verify her password with him ' ' just to double check our records. ' ' Jane does not suspect anything amiss, and parts with her password. Jack can now access Brown Co. ' s computers with a valid user name and password, to steal the cookie recipe. What kind of attack is being illustrated here?
TCP SYN Flood attack uses the three-way handshake mechanism.
1. An attacker at system A sends a SYN packet to victim at system B.
2. System B sends a SYN/ACK packet to victim A.
3. As a normal three-way handshake mechanism system A should send an ACK packet to system B, however, system A does not send an ACK packet to system B. In this case client B is waiting for an ACK packet from client A.
This status of client B is called _________________
The SYN flood attack sends TCP connections requests faster than a machine can process them.
Attacker creates a random source address for each packet
SYN flag set in each packet is a request to open a new connection to the server from the spoofed IP address
Victim responds to spoofed IP address, then waits for confirmation that never arrives (timeout wait is about 3 minutes)
Victim ' s connection table fills up waiting for replies and ignores new connections
Legitimate users are ignored and will not be able to access the server
How do you protect your network against SYN Flood attacks?

