Last Update 17 hours ago Total Questions : 878
The Certified Ethical Hacker (CEH) content is now fully updated, with all current exam questions added 17 hours ago. Deciding to include CEH-001 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our CEH-001 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these CEH-001 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Certified Ethical Hacker (CEH) practice test comfortably within the allotted time.
A common technique for luring e-mail users into opening virus-launching attachments is to send messages that would appear to be relevant or important to many of their potential recipients. One way of accomplishing this feat is to make the virus-carrying messages appear to come from some type of business entity retailing sites, UPS, FEDEX, CITIBANK or a major provider of a common service.
Here is a fraudulent e-mail claiming to be from FedEx regarding a package that could not be delivered. This mail asks the receiver to open an attachment in order to obtain the FEDEX tracking number for picking up the package. The attachment contained in this type of e-mail activates a virus.
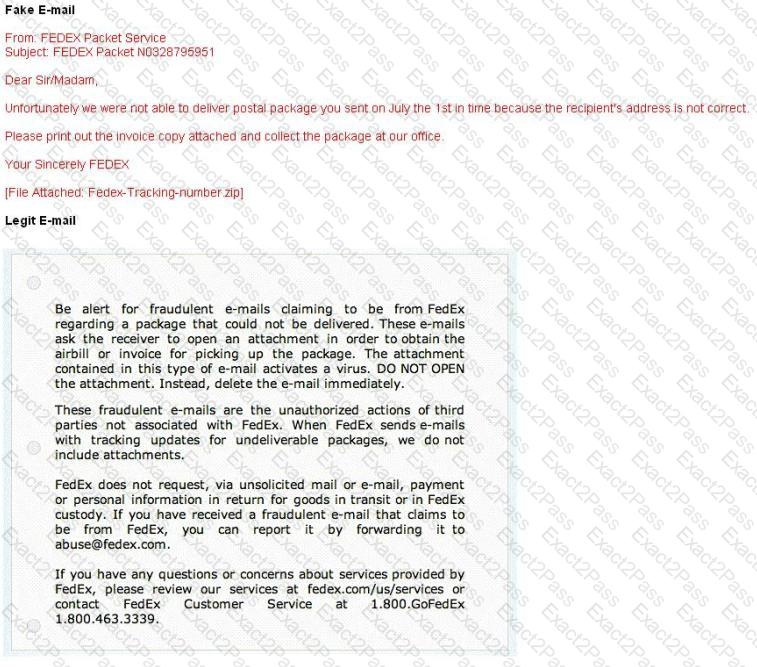
Vendors send e-mails like this to their customers advising them not to open any files attached with the mail, as they do not include attachments.
Fraudulent e-mail and legit e-mail that arrives in your inbox contain the fedex.com as the sender of the mail.
How do you ensure if the e-mail is authentic and sent from fedex.com?
David is a security administrator working in Boston. David has been asked by the office ' s manager to block all POP3 traffic at the firewall because he believes employees are spending too much time reading personal email. How can David block POP3 at the firewall?

An attacker finds a web page for a target organization that supplies contact information for the company. Using available details to make the message seem authentic, the attacker drafts e-mail to an employee on the contact page that appears to come from an individual who might reasonably request confidential information, such as a network administrator.
The email asks the employee to log into a bogus page that requests the employee ' s user name and password or click on a link that will download spyware or other malicious programming.
Google ' s Gmail was hacked using this technique and attackers stole source code and sensitive data from Google servers. This is highly sophisticated attack using zero-day exploit vectors, social engineering and malware websites that focused on targeted individuals working for the company.
What is this deadly attack called?
Which tool would be used to collect wireless packet data?
Perimeter testing means determining exactly what your firewall blocks and what it allows. To conduct a good test, you can spoof source IP addresses and source ports. Which of the following command results in packets that will appear to originate from the system at 10.8.8.8? Such a packet is useful for determining whether the firewall is allowing random packets in or out of your network.
Web servers are often the most targeted and attacked hosts on organizations ' networks. Attackers may exploit software bugs in the Web server, underlying operating system, or active content to gain unauthorized access.
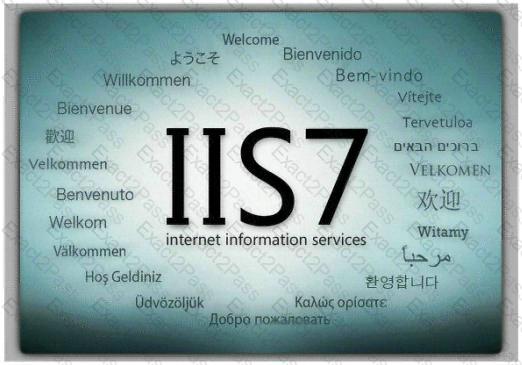
Identify the correct statement related to the above Web Server installation?
On a Linux device, which of the following commands will start the Nessus client in the background so that the Nessus server can be configured?
Which of the following types of firewall inspects only header information in network traffic?
Which of the following are password cracking tools? (Choose three.)
Least privilege is a security concept that requires that a user is
A POP3 client contacts the POP3 server:
What is a Trojan Horse?
A user on your Windows 2000 network has discovered that he can use L0phtcrack to sniff the SMB exchanges which carry user logons. The user is plugged into a hub with 23 other systems. However, he is unable to capture any logons though he knows that other users are logging in.
What do you think is the most likely reason behind this?
What hacking attack is challenge/response authentication used to prevent?
LM authentication is not as strong as Windows NT authentication so you may want to disable its use, because an attacker eavesdropping on network traffic will attack the weaker protocol. A successful attack can compromise the user ' s password. How do you disable LM authentication in Windows XP?
Eric has discovered a fantastic package of tools named Dsniff on the Internet. He has learnt to use these tools in his lab and is now ready for real world exploitation. He was able to effectively intercept communications between the two entities and establish credentials with both sides of the connections. The two remote ends of the communication never notice that Eric is relaying the information between the two.
What would you call this attack?
What happens when one experiences a ping of death?
Exhibit:
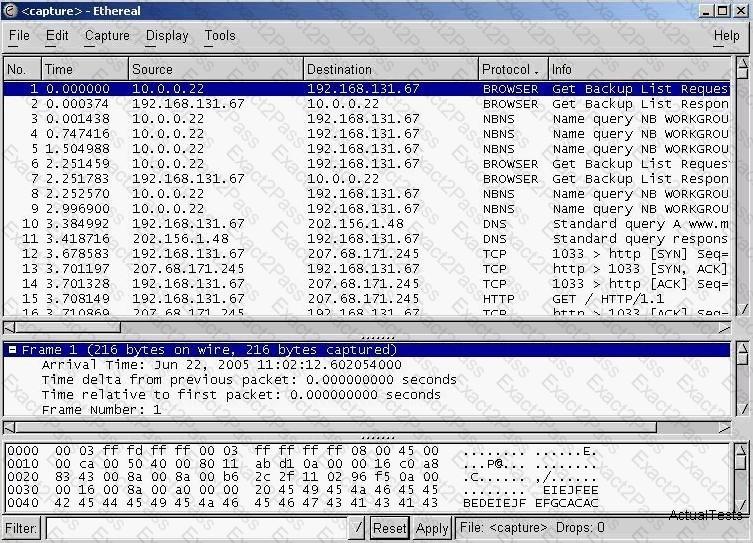
You have captured some packets in Ethereal. You want to view only packets sent from 10.0.0.22. What filter will you apply?
Susan has attached to her company’s network. She has managed to synchronize her boss’s sessions with that of the file server. She then intercepted his traffic destined for the server, changed it the way she wanted to and then placed it on the server in his home directory. What kind of attack is Susan carrying on?
Assuring two systems that are using IPSec to protect traffic over the internet, what type of general attack could compromise the data?

