Last Update 17 hours ago Total Questions : 878
The Certified Ethical Hacker (CEH) content is now fully updated, with all current exam questions added 17 hours ago. Deciding to include CEH-001 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our CEH-001 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these CEH-001 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Certified Ethical Hacker (CEH) practice test comfortably within the allotted time.
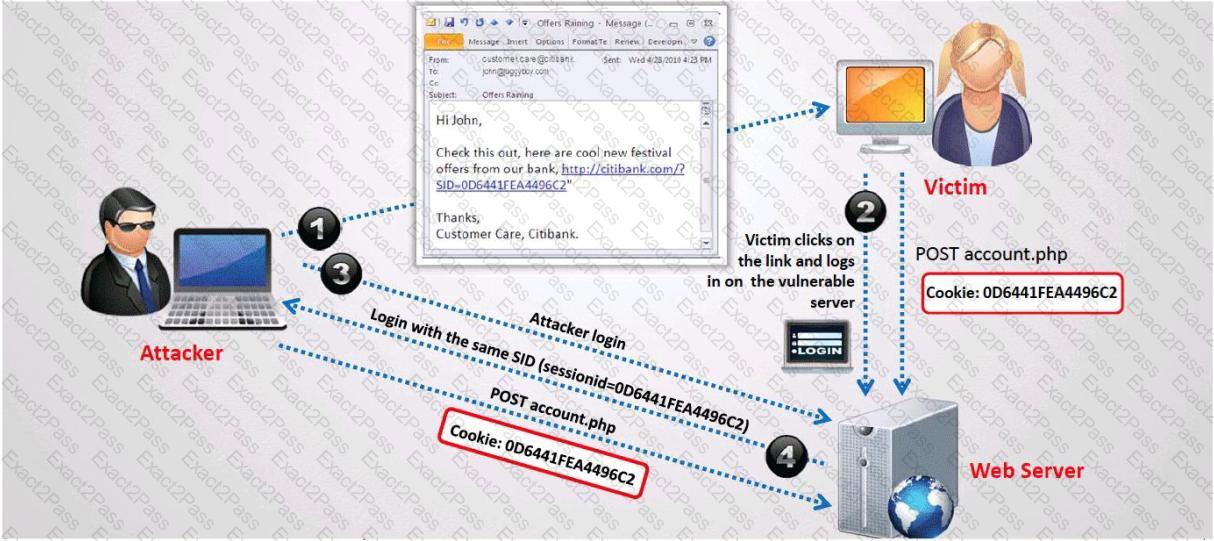
What type of session hijacking attack is shown in the exhibit?
Which of the following is used to indicate a single-line comment in structured query language (SQL)?
While checking the settings on the internet browser, a technician finds that the proxy server settings have been checked and a computer is trying to use itself as a proxy server. What specific octet within the subnet does the technician see?
A security engineer has been asked to deploy a secure remote access solution that will allow employees to connect to the company’s internal network. Which of the following can be implemented to minimize the opportunity for the man-in-the-middle attack to occur?
A certified ethical hacker (CEH) is approached by a friend who believes her husband is cheating. She offers to pay to break into her husband ' s email account in order to find proof so she can take him to court. What is the ethical response?
Every company needs a formal written document which spells out to employees precisely what they are allowed to use the company ' s systems for, what is prohibited, and what will happen to them if they break the rules. Two printed copies of the policy should be given to every employee as soon as possible after they join the organization. The employee should be asked to sign one copy, which should be safely filed by the company. No one should be allowed to use the company ' s computer systems until they have signed the policy in acceptance of its terms. What is this document called?
Which of the following cryptography attack methods is usually performed without the use of a computer?
A computer technician is using a new version of a word processing software package when it is discovered that a special sequence of characters causes the entire computer to crash. The technician researches the bug and discovers that no one else experienced the problem. What is the appropriate next step?
Rebecca is a security analyst and knows of a local root exploit that has the ability to enable local users to use available exploits to gain root privileges. This vulnerability exploits a condition in the Linux kernel within the execve() system call. There is no known workaround that exists for this vulnerability. What is the correct action to be taken by Rebecca in this situation as a recommendation to management?
If you send a SYN to an open port, what is the correct response?(Choose all correct answers.
You want to carry out session hijacking on a remote server. The server and the client are communicating via TCP after a successful TCP three way handshake. The server has just received packet #120 from the client. The client has a receive window of 200 and the server has a receive window of 250.
Within what range of sequence numbers should a packet, sent by the client fall in order to be accepted by the server?
You work as security technician at XYZ.com. While doing web application testing, you might be required to look through multiple web pages online which can take a long time. Which of the processes listed below would be a more efficient way of doing this type of validation?
You visit a website to retrieve the listing of a company ' s staff members. But you can not find it on the website. You know the listing was certainly present one year before. How can you retrieve information from the outdated website?
Network Intrusion Detection systems can monitor traffic in real time on networks.
Which one of the following techniques can be very effective at avoiding proper detection?
Tess King is making use of Digest Authentication for her Web site. Why is this considered to be more secure than Basic authentication?
Bubba has just accessed he preferred ecommerce web site and has spotted an item that he would like to buy. Bubba considers the price a bit too steep. He looks at the source code of the webpage and decides to save the page locally, so that he can modify the page variables. In the context of web application security, what do you think Bubba has changes?
Jackson discovers that the wireless AP transmits 128 bytes of plaintext, and the station responds by encrypting the plaintext. It then transmits the resulting ciphertext using the same key and cipher that are used by WEP to encrypt subsequent network traffic. What authentication mechanism is being followed here?
If an attacker ' s computer sends an IPID of 31400 to a zombie (Idle Scanning) computer on an open port, what will be the response?
Which of the following is a common Service Oriented Architecture (SOA) vulnerability?
One of the ways to map a targeted network for live hosts is by sending an ICMP ECHO request to the broadcast or the network address. The request would be broadcasted to all hosts on the targeted network. The live hosts will send an ICMP ECHO Reply to the attacker ' s source IP address.
You send a ping request to the broadcast address 192.168.5.255.
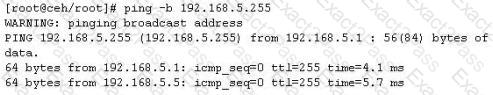
There are 40 computers up and running on the target network. Only 13 hosts send a reply while others do not. Why?

