Last Update 16 hours ago Total Questions : 32
The FCSS - Security Operations 7.4 Analyst content is now fully updated, with all current exam questions added 16 hours ago. Deciding to include FCSS_SOC_AN-7.4 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our FCSS_SOC_AN-7.4 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these FCSS_SOC_AN-7.4 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any FCSS - Security Operations 7.4 Analyst practice test comfortably within the allotted time.
Which two statements about the FortiAnalyzer Fabric topology are true? (Choose two.)
When configuring a FortiAnalyzer to act as a collector device, which two steps must you perform? (Choose two.)
Which three end user logs does FortiAnalyzer use to identify possible IOC compromised hosts? (Choose three.)
Review the following incident report:
Attackers leveraged a phishing email campaign targeting your employees.
The email likely impersonated a trusted source, such as the IT department, and requested login credentials.
An unsuspecting employee clicked a malicious link in the email, leading to the download and execution of a Remote Access Trojan (RAT).
The RAT provided the attackers with remote access and a foothold in the compromised system.
Which two MITRE ATT & CK tactics does this incident report capture? (Choose two.)
Refer to the exhibits.
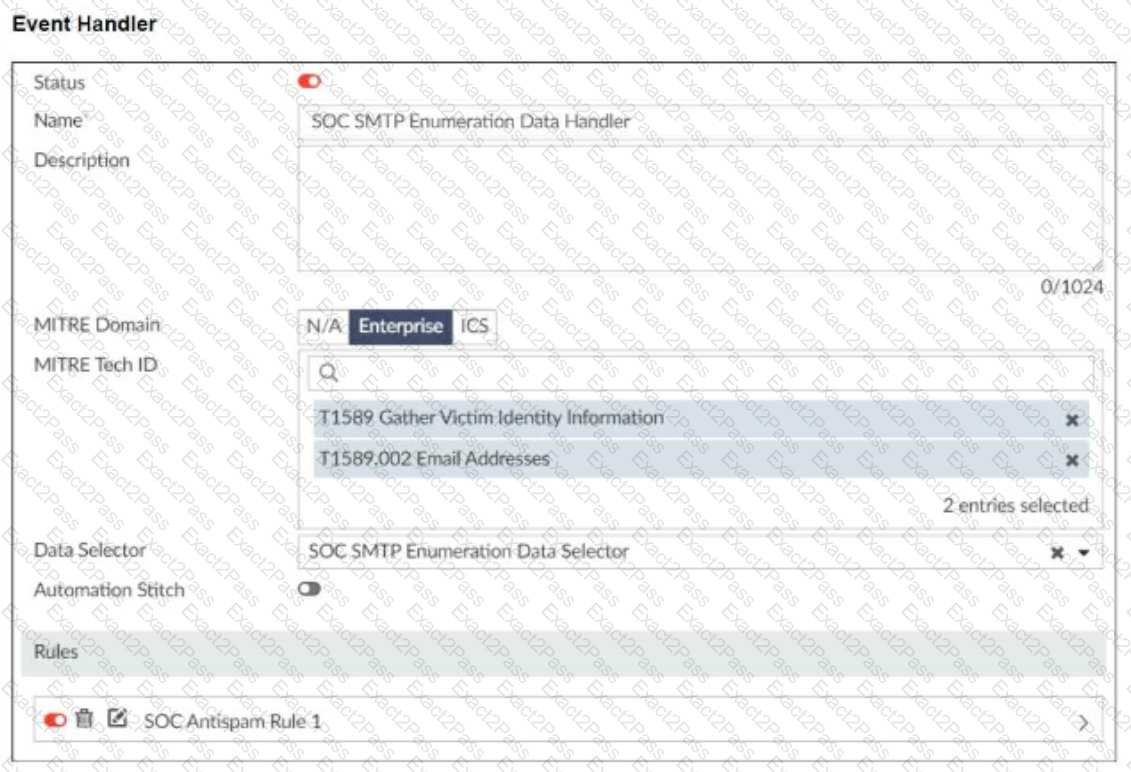
You configured a custom event handler and an associated rule to generate events whenever FortiMail detects spam emails. However, you notice that the event handler is generating events for both spam emails and clean emails.
Which change must you make in the rule so that it detects only spam emails?
Refer to the exhibit,

which shows the partial output of the MITRE ATT & CK Enterprise matrix on FortiAnalyzer.
Which two statements are true? (Choose two.)

