Last Update 17 hours ago Total Questions : 322
The HCIE-Datacom V1.0 content is now fully updated, with all current exam questions added 17 hours ago. Deciding to include H12-891_V1.0 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our H12-891_V1.0 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these H12-891_V1.0 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any HCIE-Datacom V1.0 practice test comfortably within the allotted time.
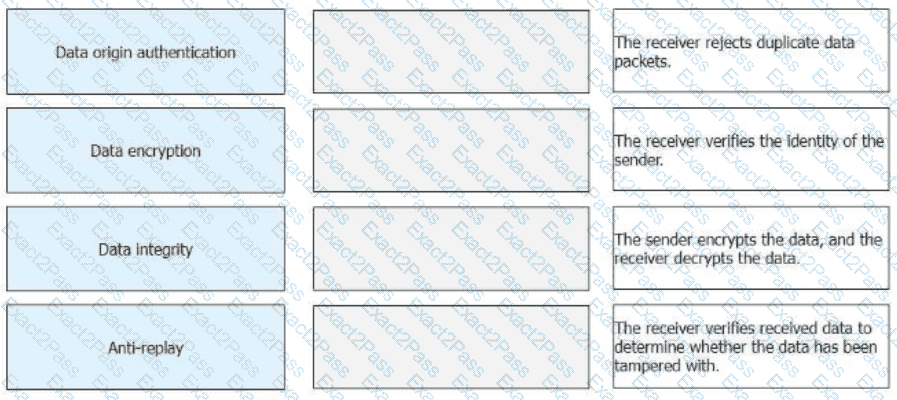
Drag the IPsec functions on the left to the corresponding function description on the right.
When Huawei iMaster NCE-IP is used to configure SR-MPLS TE tunnels, which of the following protocols is used by the controller to collect device running status information?
An SRv6 Policy can be either statically configured on a device, or be delivered to a device after being dynamically generated by the controller.
The command can be run to completely isolate Layer 2 and Layer 3 of different interfaces in a VLAN. (Use lowercase letters to supplement the command, which cannot be abbreviated.)
What can be determined from the following figure?
< R1 > display bgp ipv6 routing-table
Total Number of Routes: 2
* > i Network : 3002::3
NextHop : 3000:FDEA::3
MED : 0
Path/Orgn : i
* > i Network : 3002::4
NextHop : 3000:FDEA::3
MED : 0
PrefixLen : 128
LocPrf : 100
PrefVal : 0
Path/Orgn : 65001 i
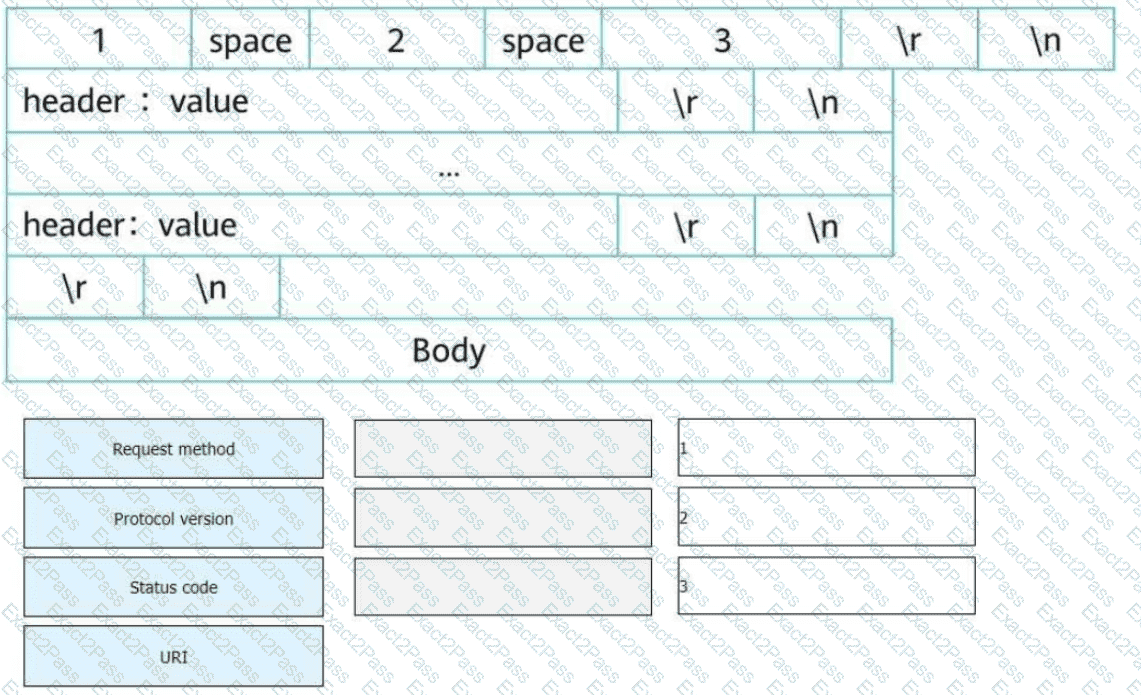
An HTTP request line consists of three fields. Select the fields to form a complete HTTP request message.
MACsec can provide secure services during MAC-layer data transmitting and receiving. Which of the following services is not provided by MACsec?
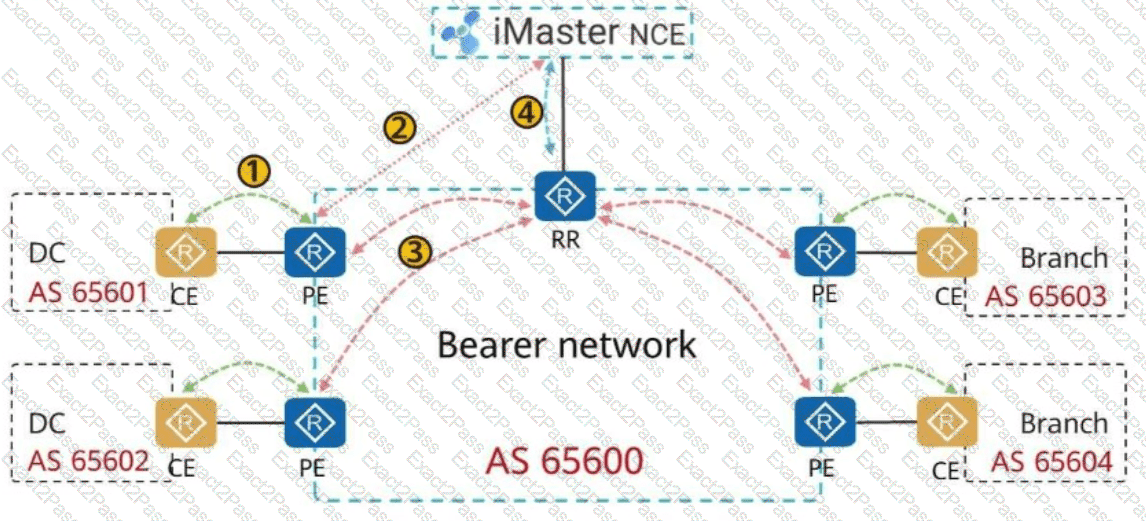
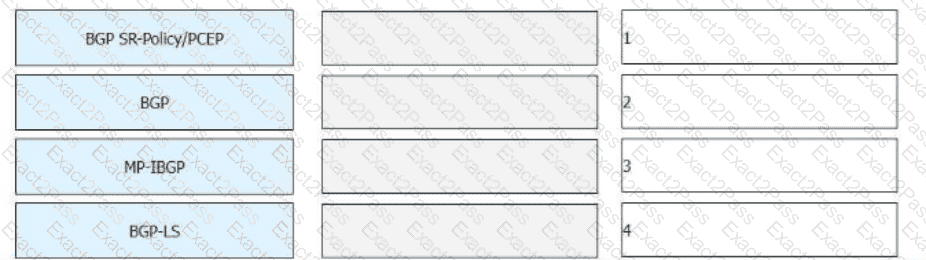
On the bearer WAN shown in the figure, SR (Segment Routing) is deployed, and the controller is used to compute paths. Drag network technologies on the left to the corresponding application locations on the right.
IPsec uses an asymmetric encryption algorithm to encrypt the symmetric algorithm key, which it uses to encrypt/decrypt data, ensuring security and performance.
In the LDP session establishment process, the initiator sends an Initialization message for parameter negotiation. Which message will be sent by the responder if it does not accept negotiation parameters?

