Last Update 10 hours ago Total Questions : 167
The Aruba Certified Network Security Associate Exam content is now fully updated, with all current exam questions added 10 hours ago. Deciding to include HPE6-A78 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our HPE6-A78 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these HPE6-A78 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Aruba Certified Network Security Associate Exam practice test comfortably within the allotted time.
Your Aruba Mobility Master-based solution has detected a suspected rogue AP. Among other information, the ArubaOS Detected Radios page lists this information for the AP:
SSID = PublicWiFi
BSSID = a8:bd:27:12:34:56
Match method = Plus one
Match method = Eth-Wired-Mac-Table
The security team asks you to explain why this AP is classified as a rogue. What should you explain?
What is a reason to set up a packet capture on an Aruba Mobility Controller (MC)?
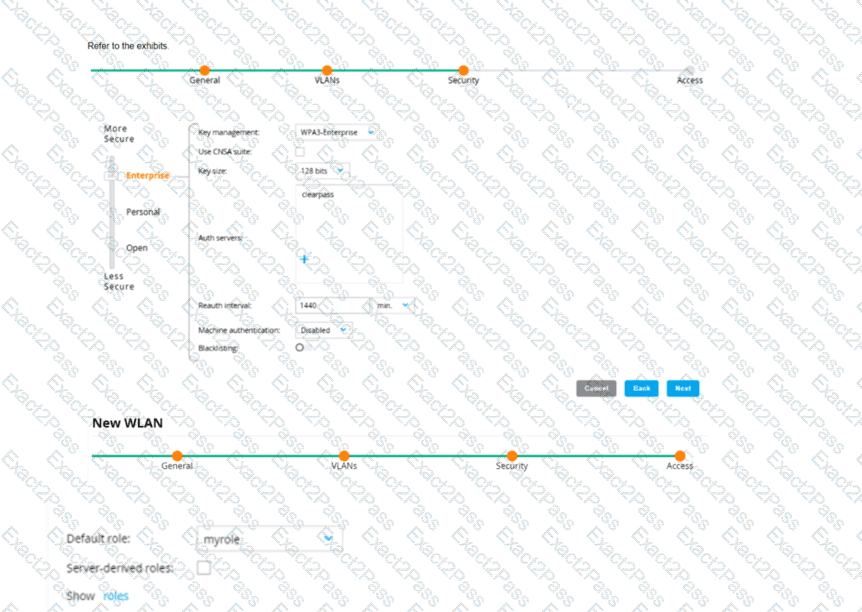
An admin has created a WLAN that uses the settings shown in the exhibits (and has not otherwise adjusted the settings in the AAA profile) A client connects to the WLAN Under which circumstances will a client receive the default role assignment?
Your AOS solution has detected a rogue AP with Wireless Intrusion Prevention (WIP). Which information about the detected radio can best help you to locate the rogue device?
What is one benefit of enabling Enhanced Secure mode on an ArubaOS-Switch?
An AOS-CX switch currently has no device fingerprinting settings configured on it. You want the switch to start collecting DHCP and LLDP information. You enter these commands:
Switch(config)# client device-fingerprint profile myprofile
Switch(myprofile)# dhcp
Switch(myprofile)# lldp
What else must you do to allow the switch to collect information from clients?
What does the NIST model for digital forensics define?
A client is connected to a Mobility Controller (MC). These firewall rules apply to this client’s role:
ipv4 any any svc-dhcp permit
ipv4 user 10.5.5.20 svc-dns permit
ipv4 user 10.1.5.0 255.255.255.0 https permit
ipv4 user 10.1.0.0 255.255.0.0 https deny_opt
ipv4 user any any permit
What correctly describes how the controller treats HTTPS packets to these two IP addresses, both of which are on the other side of the firewall:
10.1.20.1
10.5.5.20
An ArubaOS-CX switch enforces 802.1X on a port. No fan-through options or port-access roles are configured on the port The 802 1X supplicant on a connected client has not yet completed authentication
Which type of traffic does the authenticator accept from the client?
What is one way a noneypot can be used to launch a man-in-the-middle (MITM) attack to wireless clients?

