Last Update 10 hours ago Total Questions : 167
The Aruba Certified Network Security Associate Exam content is now fully updated, with all current exam questions added 10 hours ago. Deciding to include HPE6-A78 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our HPE6-A78 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these HPE6-A78 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Aruba Certified Network Security Associate Exam practice test comfortably within the allotted time.
Refer to the exhibit.
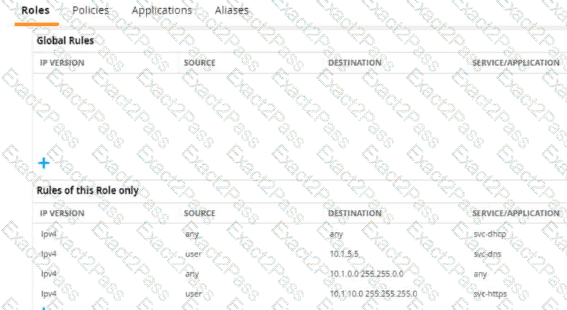
A diem is connected to an ArubaOS Mobility Controller. The exhibit snows all Tour firewall rules that apply to this diem
What correctly describes how the controller treats HTTPS packets to these two IP addresses, both of which are on the other side of the firewall
10.1 10.10
203.0.13.5
What is a benefit of Protected Management Frames (PMF). sometimes called Management Frame Protection (MFP)?
You are managing an Aruba Mobility Controller (MC). What is a reason for adding a " Log Settings " definition in the ArubaOS Diagnostics > System > Log Settings page?
You have configured a WLAN to use Enterprise security with the WPA3 version.
How does the WLAN handle encryption?
How can hackers implement a man-in-the-middle (MITM) attack against a wireless client?
What is a use case for Transport Layer Security (TLS)?
A company is deploying AOS-CX switches to support 114 employees, which will tunnel client traffic to an HPE Aruba Networking Mobility Controller (MC) for the MC to apply firewall policies and deep packet inspection (DPI). This MC will be dedicated to receiving traffic from the AOS-CX switches.
What are the licensing requirements for the MC?
A company with 465 employees wants to deploy an open WLAN for guests. The company wants the experience to be as follows:
Guests select the WLAN and connect without having to enter a password.
Guests are redirected to a welcome web page and log in. The company also wants to provide encryption for the network for devices that are capable. Which security options should you implement for the WLAN?
You have been asked to send RADIUS debug messages from an AOS-CX switch to a central SIEM server at 10.5.15.6. The server is already defined on the switch with this command:
logging 10.5.15.6
You enter this command:
debug radius all
What is the correct debug destination?
What distinguishes a Distributed Denial of Service (DDoS) attack from a traditional Denial of Service (DoS) attack?

